【APP逆向】某某听书app逆向分析
声明
本文章中所有内容仅供学习交流使用,不用于其他任何目的,不提供完整代码,抓包内容、敏感网址、数据接口等均已做脱敏处理,严禁用于商业用途和非法用途,否则由此产生的一切后果均与作者无关! 本文章未经许可禁止转载,禁止任何修改后二次传播,擅自使用本文讲解的技术而导致的任何意外,作者均不负责,若有侵权,请联系, 请在公众号【逆向指南】联系作者立即删除
逆向目标
-
目标 某某听书 -
版本 9.4.50.3 -
逆向参数 signature
抓包分析
使用小黄鸟配合手机抓包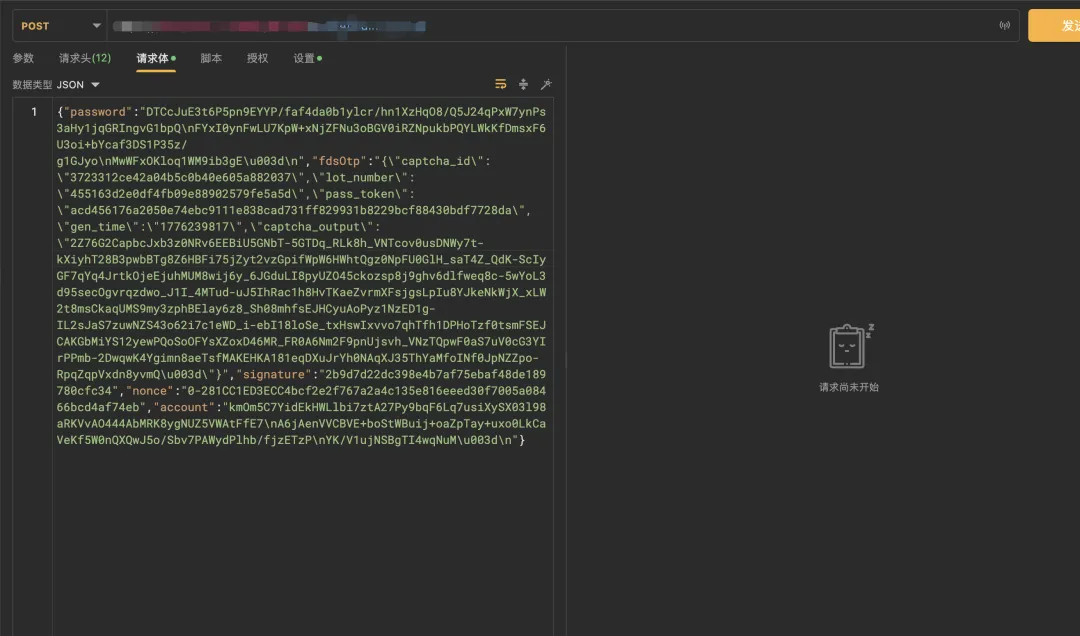 分析这个signature参数
分析这个signature参数
java 层分析
使用frida来hook HashMap
functionmain(){ Java.perform(function () { var hashMap = Java.use("java.util.HashMap"); hashMap.put.implementation = function (a,b){ console.log('输出--》',a,b)if(a=="signature"){ showStacks() }return this.put(a,b) } })}functionshowStacks() { Java.perform(function () { console.log(Java.use("android.util.Log").getStackTraceString( Java.use("java.lang.Throwable").$new() ));})}main()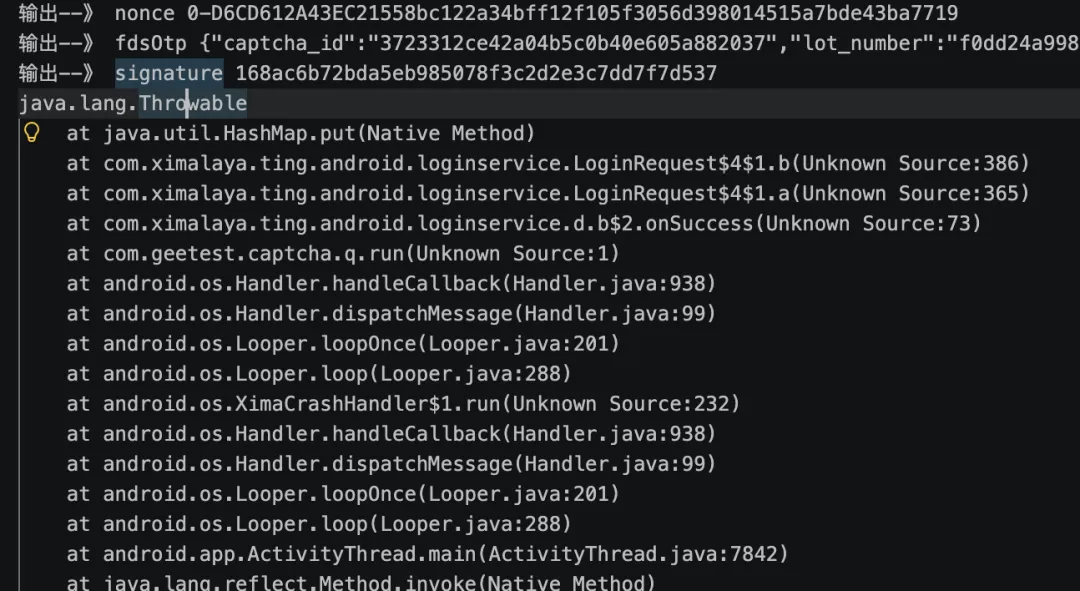 经过输出的日志分析出
经过输出的日志分析出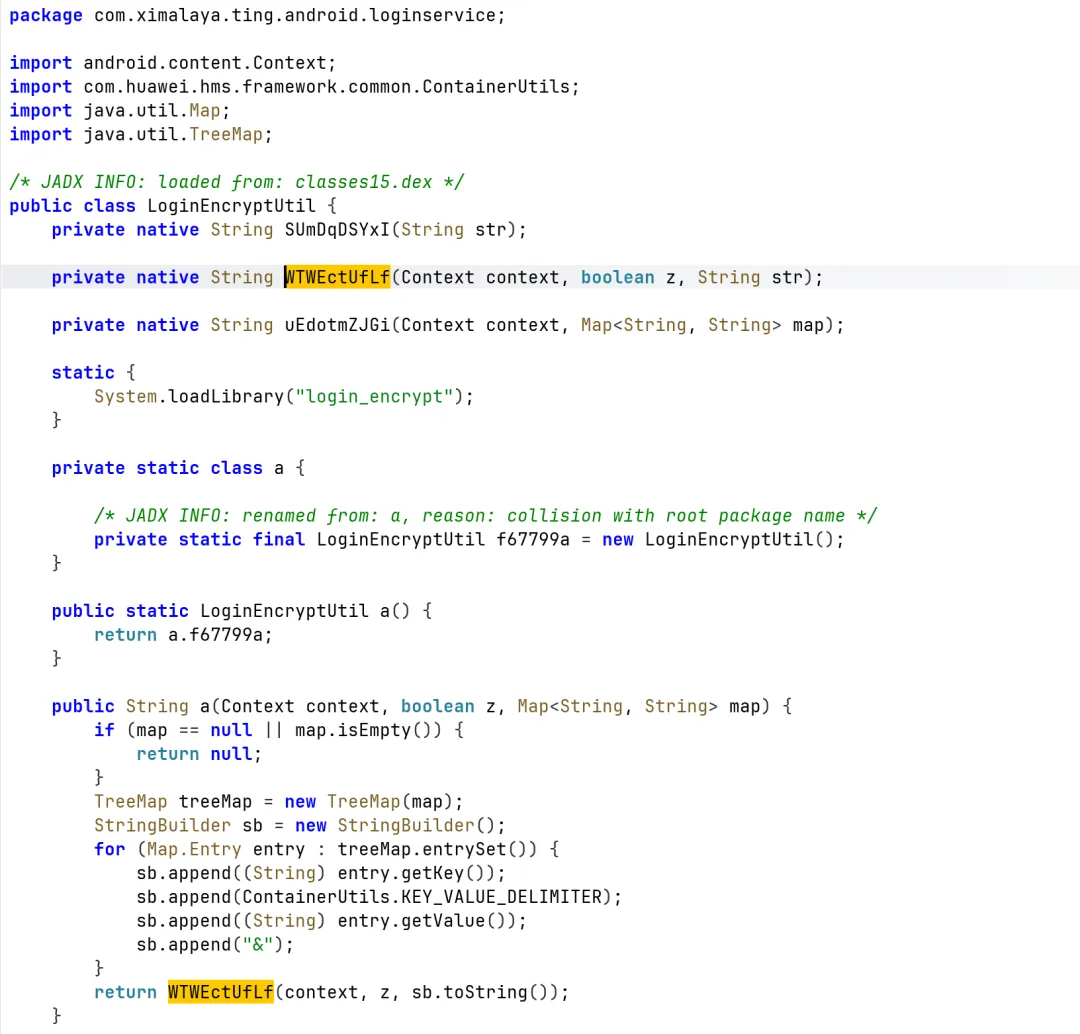 这个WTWEctUfLf是最终加密的位置 so login_encrypt 是使用frida hook WTWEctUfLf,参数是
这个WTWEctUfLf是最终加密的位置 so login_encrypt 是使用frida hook WTWEctUfLf,参数是
[*] hook_mointor_WTWEctUfLf is injected![->] com_ximalaya_ting_android_loginservice_LoginEncryptUtil.WTWEctUfLf is called! args are as follows: ->context= com.ximalaya.ting.android.xmloader.XMApplication@1aac5ef ->z= false ->str= account=E8sZy+hZzthmH8h/ynoG2uqlcQjUvAzi9zxU+slXGwTdrhf5Cu94kdStFEB30iVAfxqBN7wjpg1wK2LE76p22QPdtbeUZwCwR4xivGRps3uy5+G2QiQxLNtYlpaBsEJRQwSqq8PW9pEIv+WR3FjdUAf4qH7rExziwaGy5HIIi5o=&fdsOtp={"captcha_id":"3723312ce42a04b5c0b40e605a882037","lot_number":"bd948084401f486b933734c8272cd5d8","pass_token":"1f7d6eb1b4b0a77ca4b678fb4dc71ba0fb882366dc9293a71fac693bb7a1b402","gen_time":"1776074775","captcha_output":"2Z76G2CapbcJxb3z0NRv6MAavUgVwwmFweN6_LK9stpxnNF_skXR6eHM_SyoutMoj0e-aw1Z4PBgLFFmw0YGlvRUy-6VZwZuJtCWV5jNFtr5abzMM29yc66oT4qRbGTMVq6j1wZpN3Deju4nmSlH2nk6lUH9mHtSDSWr8VEzCf6GEdqMFJK9Is3u3mrkTcVS3y7-PpfEqegvKMalfYR2taLuXcKsRYCADluELyw_HB6hBRlqhKXTXKnr4VGxWXLkf7hR8qFnKlY4ZfVLXGZQpSFLeBzZ5-QkHCi2lA9jUw9Ron_TNlvgOPv6yqLP8d2-U-FFCG1qH0iFOH0vl5EaME22A9u6fxTMRW6LH3aWP7fgNxJL7C1wJu8CQTgBcT7Byl0Bwbbmg5pwdAzudiIbFe2MPqhOr1U8f_VRfRrZ3zT_lmYL_JvqukmxVKmrJ5rmEDNiAsFQTDB7rI86u-uvmQY60hSd98_mOURwjvdfTynGcmS8XmFoTsIe1e5OzdwqY3qOPXipe7o_z6GMlN7XFZGPl8CdAHDzS5hJgp9-2c0="}&nonce=0-DEDB11BE0E7E60b30d6f698ac13d2e392d54862a583e1f38e034f9583b156f&password=W27HC5G4WQoTRsyxD9P+6wM71UNIN9Ki2eL8qVUGOnbDzr5+zel+QdlGfVhOdI9JFxUCN9rbFNAKtEXF++07ujriurJa+WwYtdfOw6pS5g+J//x1cYhJ6sgWgZ685WwwU/htUcIVBQkODHhV8S9WanHPTFJgrEaBoYQVrxYQsQ0=&[<-] com_ximalaya_ting_android_loginservice_LoginEncryptUtil.WTWEctUfLf ended! retval= 1152dec4db4ac1f301d93f78d6fdaefd1654bebf使用unidbg补环境
基本配置
public class Ximalaya extends AbstractJni { private static AndroidEmulator emulator; private static Module module; private final DvmClass cSignUtil; private final VM vm; public Ximalaya(){ emulator = AndroidEmulatorBuilder.for32Bit() .setProcessName("com.ximalaya.ting.android") .build(); Memory memory = emulator.getMemory(); memory.setLibraryResolver(new AndroidResolver(23)); vm = emulator.createDalvikVM( new File("/Users/mac/unidbg-file/unidbg9.9/lib/com.ximalaya.ting.android/106_24b6f7c96c805273380c4e16230fdb53.apk")); vm.setVerbose(true); vm.setJni(this); DalvikModule dm = vm.loadLibrary(new File("/Users/mac/unidbg-file/unidbg9.9/lib/com.ximalaya.ting.android/liblogin_encrypt.so"), false); cSignUtil = vm.resolveClass("com/ximalaya/ting/android/loginservice/LoginEncryptUtil"); dm.callJNI_OnLoad(emulator); module = dm.getModule(); } void get_sign(){ String methodSign = "WTWEctUfLf(Landroid/content/Context;ZLjava/lang/String;)Ljava/lang/String;"; // 👉 你 hook 到的参数 String str = "account=E8sZy+hZzthmH8h/ynoG2uqlcQjUvAzi9zxU+slXGwTdrhf5Cu94kdStFEB30iVAfxqBN7wjpg1w\n" +"K2LE76p22QPdtbeUZwCwR4xivGRps3uy5+G2QiQxLNtYlpaBsEJRQwSqq8PW9pEIv+WR3FjdUAf4\n" +"qH7rExziwaGy5HIIi5o=\n" +"&fdsOtp={\"captcha_id\":\"3723312ce42a04b5c0b40e605a882037\",\"lot_number\":\"bd948084401f486b933734c8272cd5d8\",\"pass_token\":\"1f7d6eb1b4b0a77ca4b678fb4dc71ba0fb882366dc9293a71fac693bb7a1b402\",\"gen_time\":\"1776074775\",\"captcha_output\":\"2Z76G2CapbcJxb3z0NRv6MAavUgVwwmFweN6_LK9stpxnNF_skXR6eHM_SyoutMoj0e-aw1Z4PBgLFFmw0YGlvRUy-6VZwZuJtCWV5jNFtr5abzMM29yc66oT4qRbGTMVq6j1wZpN3Deju4nmSlH2nk6lUH9mHtSDSWr8VEzCf6GEdqMFJK9Is3u3mrkTcVS3y7-PpfEqegvKMalfYR2taLuXcKsRYCADluELyw_HB6hBRlqhKXTXKnr4VGxWXLkf7hR8qFnKlY4ZfVLXGZQpSFLeBzZ5-QkHCi2lA9jUw9Ron_TNlvgOPv6yqLP8d2-U-FFCG1qH0iFOH0vl5EaME22A9u6fxTMRW6LH3aWP7fgNxJL7C1wJu8CQTgBcT7Byl0Bwbbmg5pwdAzudiIbFe2MPqhOr1U8f_VRfRrZ3zT_lmYL_JvqukmxVKmrJ5rmEDNiAsFQTDB7rI86u-uvmQY60hSd98_mOURwjvdfTynGcmS8XmFoTsIe1e5OzdwqY3qOPXipe7o_z6GMlN7XFZGPl8CdAHDzS5hJgp9-2c0=\"}&nonce=0-DEDB11BE0E7E60b30d6f698ac13d2e392d54862a583e1f38e034f9583b156f&password=W27HC5G4WQoTRsyxD9P+6wM71UNIN9Ki2eL8qVUGOnbDzr5+zel+QdlGfVhOdI9JFxUCN9rbFNAK\n" +"tEXF++07ujriurJa+WwYtdfOw6pS5g+J//x1cYhJ6sgWgZ685WwwU/htUcIVBQkODHhV8S9WanHP\n" +"TFJgrEaBoYQVrxYQsQ0=\n" +"&"; String str1 = "1" ; StringObject jStr = new StringObject(vm, str); boolean z = false; DvmObject<?> contextClass = vm.resolveClass("android/content/ContextWrapper").newObject(null); // 👉 调用 JNI 方法 String result = cSignUtil.callStaticJniMethodObject( emulator, methodSign, contextClass, z, jStr ).getValue().toString(); System.out.println("🔥 sign = " + result); } public static void main(String[] args) throws FileNotFoundException { Ximalaya ximalaya = new Ximalaya(); ximalaya.get_sign(); }这个是需要补包名
java.lang.UnsupportedOperationException: java/lang/String->toUpperCase()Ljava/lang/String; at com.github.unidbg.linux.android.dvm.AbstractJni.callObjectMethod(AbstractJni.java:1427)@Override public DvmObject<?> callObjectMethod(BaseVM vm, DvmObject<?> dvmObject, String signature, VarArg varArg) { switch (signature){case"android/content/ContextWrapper->getPackageName()Ljava/lang/String;":return new StringObject(vm,"com.ximalaya.ting.android"); }java.lang.UnsupportedOperationException: java/lang/String->toUpperCase()Ljava/lang/String; at com.github.unidbg.linux.android.dvm.AbstractJni.callObjectMethod(AbstractJni.java:1427) 这样补case"java/lang/String->toUpperCase()Ljava/lang/String;": String value = (String) dvmObject.getValue();return new StringObject(vm, value.toUpperCase());java.lang.UnsupportedOperationException: java/lang/StringBuilder-><init>()V at com.github.unidbg.linux.android.dvm.AbstractJni.newObject(AbstractJni.java:1123) 这样补case"java/lang/StringBuilder->append(Ljava/lang/String;)Ljava/lang/StringBuilder;": StringBuilder sb = (StringBuilder) dvmObject.getValue(); String str = (String) varArg.getObjectArg(0).getValue(); sb.append(str);return dvmObject; 先不带的大家一起补了,剩下了的环境都很简单,你门先自己补不会补在看我的代码
补环境的代码
@Override public DvmObject<?> callObjectMethod(BaseVM vm, DvmObject<?> dvmObject, String signature, VarArg varArg) { switch (signature){case"android/content/ContextWrapper->getPackageName()Ljava/lang/String;":return new StringObject(vm,"com.ximalaya.ting.android");case"java/lang/String->toUpperCase()Ljava/lang/String;": String value = (String) dvmObject.getValue();return new StringObject(vm, value.toUpperCase());case"java/security/MessageDigest->digest()[B": MessageDigest md = (MessageDigest) dvmObject.getValue();return new ByteArray(vm, md.digest());case"java/lang/StringBuilder->append(Ljava/lang/String;)Ljava/lang/StringBuilder;": StringBuilder sb = (StringBuilder) dvmObject.getValue(); String str = (String) varArg.getObjectArg(0).getValue(); sb.append(str);return dvmObject;case"java/lang/StringBuilder->append(I)Ljava/lang/StringBuilder;": StringBuilder sb1 = (StringBuilder) dvmObject.getValue(); int value1 = varArg.getIntArg(0); sb1.append(value1);return dvmObject;case"java/lang/StringBuilder->toString()Ljava/lang/String;": { StringBuilder sb2 = (StringBuilder) dvmObject.getValue();return new StringObject(vm, sb2.toString()); } }return super.callObjectMethod(vm, dvmObject, signature, varArg); } @Override public DvmObject<?> newObject(BaseVM vm, DvmClass dvmClass, String signature, VarArg varArg) { switch (signature){case"java/lang/StringBuilder-><init>()V":return vm.resolveClass("java/lang/StringBuilder") .newObject(new StringBuilder()); }return super.newObject(vm, dvmClass, signature, varArg); } @Override public DvmObject<?> callStaticObjectMethod(BaseVM vm, DvmClass dvmClass, String signature, VarArg varArg) { switch (signature){case"java/security/MessageDigest->getInstance(Ljava/lang/String;)Ljava/security/MessageDigest;": String algorithm = varArg.getObjectArg(0).getValue().toString(); System.out.println("MessageDigest.getInstance => " + algorithm); try { MessageDigest md = MessageDigest.getInstance(algorithm); // 返回一个 Java层包装对象return vm.resolveClass("java/security/MessageDigest") .newObject(md); } catch (Exception e) { throw new IllegalStateException(e); }case"java/lang/Integer->toHexString(I)Ljava/lang/String;": int value = varArg.getIntArg(0);return new StringObject(vm, Integer.toHexString(value)); }return super.callStaticObjectMethod(vm, dvmClass, signature, varArg); } @Override public void callVoidMethod(BaseVM vm, DvmObject<?> dvmObject, String signature, VarArg varArg) { switch (signature){case"java/security/MessageDigest->update([B)V": MessageDigest md = (MessageDigest) dvmObject.getValue(); byte[] data = (byte[]) varArg.getObjectArg(0).getValue(); md.update(data);return; } super.callVoidMethod(vm, dvmObject, signature, varArg); } @Override public int callIntMethod(BaseVM vm, DvmObject<?> dvmObject, String signature, VarArg varArg) { switch (signature){case"java/lang/String->length()I":return ((String) dvmObject.getValue()).length(); }return super.callIntMethod(vm, dvmObject, signature, varArg); }生成的signature 也是跟hook 出来的一样说明unidbg补的环境没有问题
[*] hook_mointor_WTWEctUfLf is injected![->] com_ximalaya_ting_android_loginservice_LoginEncryptUtil.WTWEctUfLf is called! args are as follows: ->context= com.ximalaya.ting.android.xmloader.XMApplication@1aac5ef ->z= false ->str= account=E8sZy+hZzthmH8h/ynoG2uqlcQjUvAzi9zxU+slXGwTdrhf5Cu94kdStFEB30iVAfxqBN7wjpg1wK2LE76p22QPdtbeUZwCwR4xivGRps3uy5+G2QiQxLNtYlpaBsEJRQwSqq8PW9pEIv+WR3FjdUAf4qH7rExziwaGy5HIIi5o=&fdsOtp={"captcha_id":"3723312ce42a04b5c0b40e605a882037","lot_number":"bd948084401f486b933734c8272cd5d8","pass_token":"1f7d6eb1b4b0a77ca4b678fb4dc71ba0fb882366dc9293a71fac693bb7a1b402","gen_time":"1776074775","captcha_output":"2Z76G2CapbcJxb3z0NRv6MAavUgVwwmFweN6_LK9stpxnNF_skXR6eHM_SyoutMoj0e-aw1Z4PBgLFFmw0YGlvRUy-6VZwZuJtCWV5jNFtr5abzMM29yc66oT4qRbGTMVq6j1wZpN3Deju4nmSlH2nk6lUH9mHtSDSWr8VEzCf6GEdqMFJK9Is3u3mrkTcVS3y7-PpfEqegvKMalfYR2taLuXcKsRYCADluELyw_HB6hBRlqhKXTXKnr4VGxWXLkf7hR8qFnKlY4ZfVLXGZQpSFLeBzZ5-QkHCi2lA9jUw9Ron_TNlvgOPv6yqLP8d2-U-FFCG1qH0iFOH0vl5EaME22A9u6fxTMRW6LH3aWP7fgNxJL7C1wJu8CQTgBcT7Byl0Bwbbmg5pwdAzudiIbFe2MPqhOr1U8f_VRfRrZ3zT_lmYL_JvqukmxVKmrJ5rmEDNiAsFQTDB7rI86u-uvmQY60hSd98_mOURwjvdfTynGcmS8XmFoTsIe1e5OzdwqY3qOPXipe7o_z6GMlN7XFZGPl8CdAHDzS5hJgp9-2c0="}&nonce=0-DEDB11BE0E7E60b30d6f698ac13d2e392d54862a583e1f38e034f9583b156f&password=W27HC5G4WQoTRsyxD9P+6wM71UNIN9Ki2eL8qVUGOnbDzr5+zel+QdlGfVhOdI9JFxUCN9rbFNAKtEXF++07ujriurJa+WwYtdfOw6pS5g+J//x1cYhJ6sgWgZ685WwwU/htUcIVBQkODHhV8S9WanHPTFJgrEaBoYQVrxYQsQ0=&[<-] com_ximalaya_ting_android_loginservice_LoginEncryptUtil.WTWEctUfLf ended! retval= 1152dec4db4ac1f301d93f78d6fdaefd1654bebf生成的signsign = 1152dec4db4ac1f301d93f78d6fdaefd1654bebf经过unidbg 输出的日志可以看到这一些数据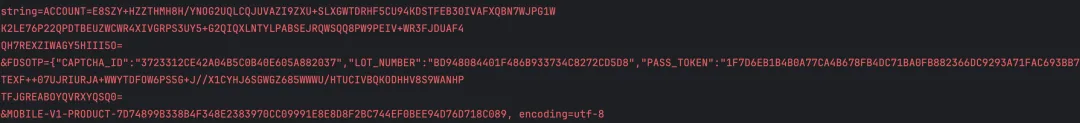 经过分析这些数据就是生成signature的参数,使用的算法也是sha1加密
经过分析这些数据就是生成signature的参数,使用的算法也是sha1加密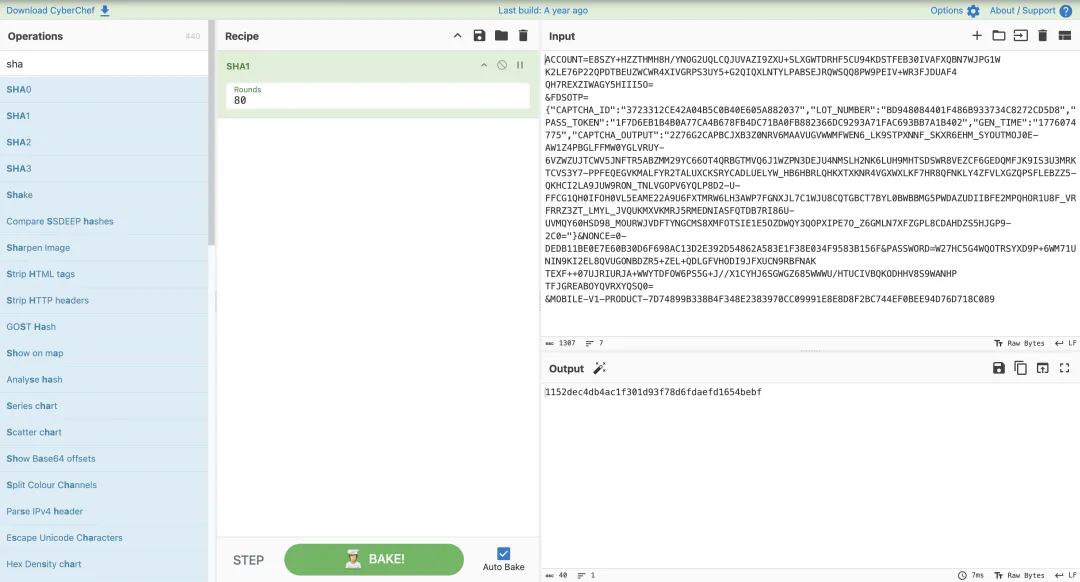 经过测试后面这些是加盐 MOBILE-V1-PRODUCT-7D74899B338B4F348E2383970CC09991E8E8D8F2BC744EF0BEE94D76D718C089 使用了1和2,来测试
经过测试后面这些是加盐 MOBILE-V1-PRODUCT-7D74899B338B4F348E2383970CC09991E8E8D8F2BC744EF0BEE94D76D718C089 使用了1和2,来测试
string=1MOBILE-V1-PRODUCT-7D74899B338B4F348E2383970CC09991E8E8D8F2BC744EF0BEE94D76D718C089, encoding=utf-863c5682f8a353abdf8b819f0c4bcbfd964cae504string=2MOBILE-V1-PRODUCT-7D74899B338B4F348E2383970CC09991E8E8D8F2BC744EF0BEE94D76D718C089, encoding=utf-82171a6d3150841aadc8b2e6bd0c896e0e4df32c8总结
这是我第一次写文章,我感觉这片文章写的不好,下一次写文章,我在慢慢改进,大家将就看一下吧
 夜雨聆风
夜雨聆风




