当前时间: 2026-03-09 21:50:02
分类:办公文件
评论(0)
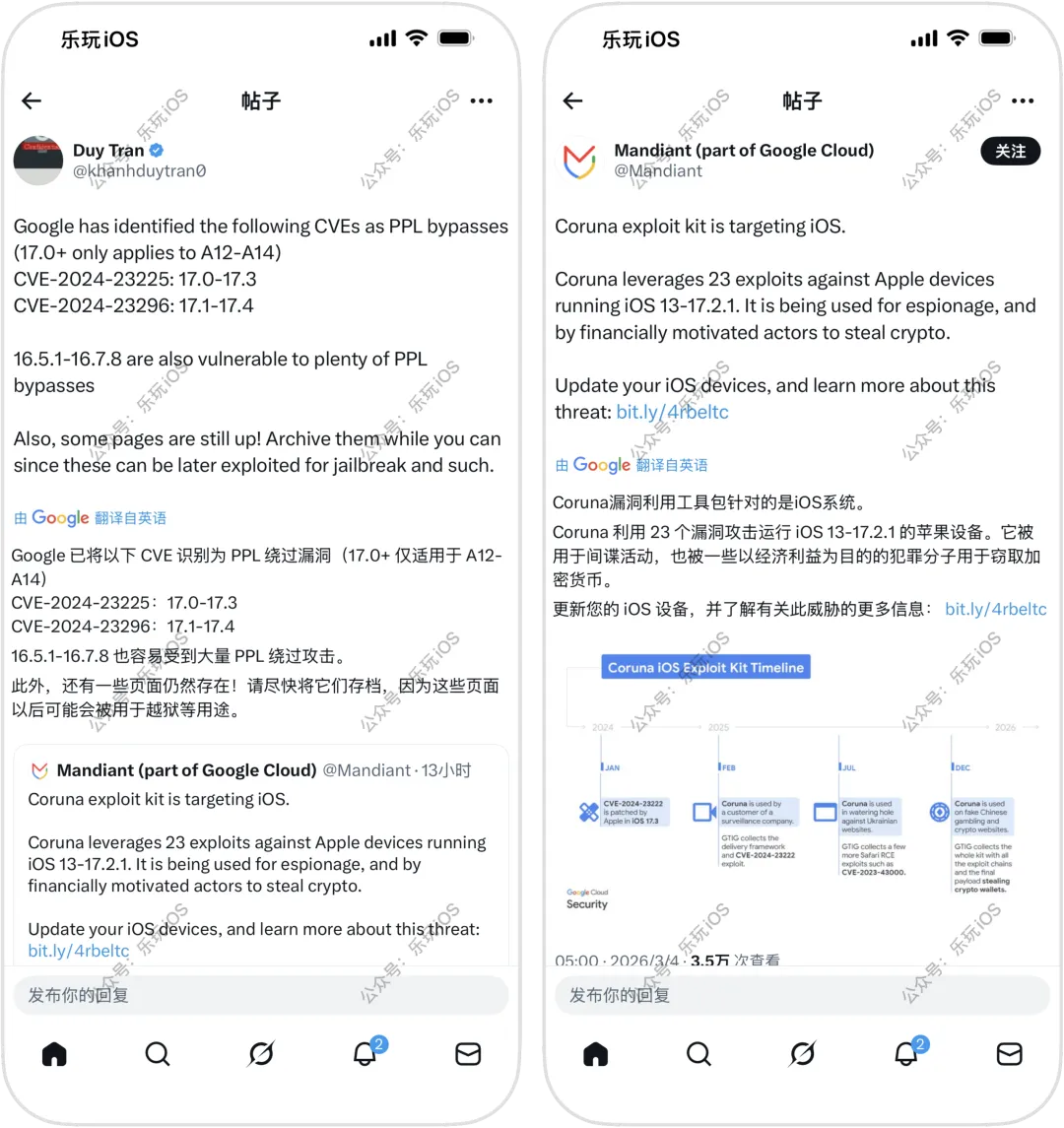
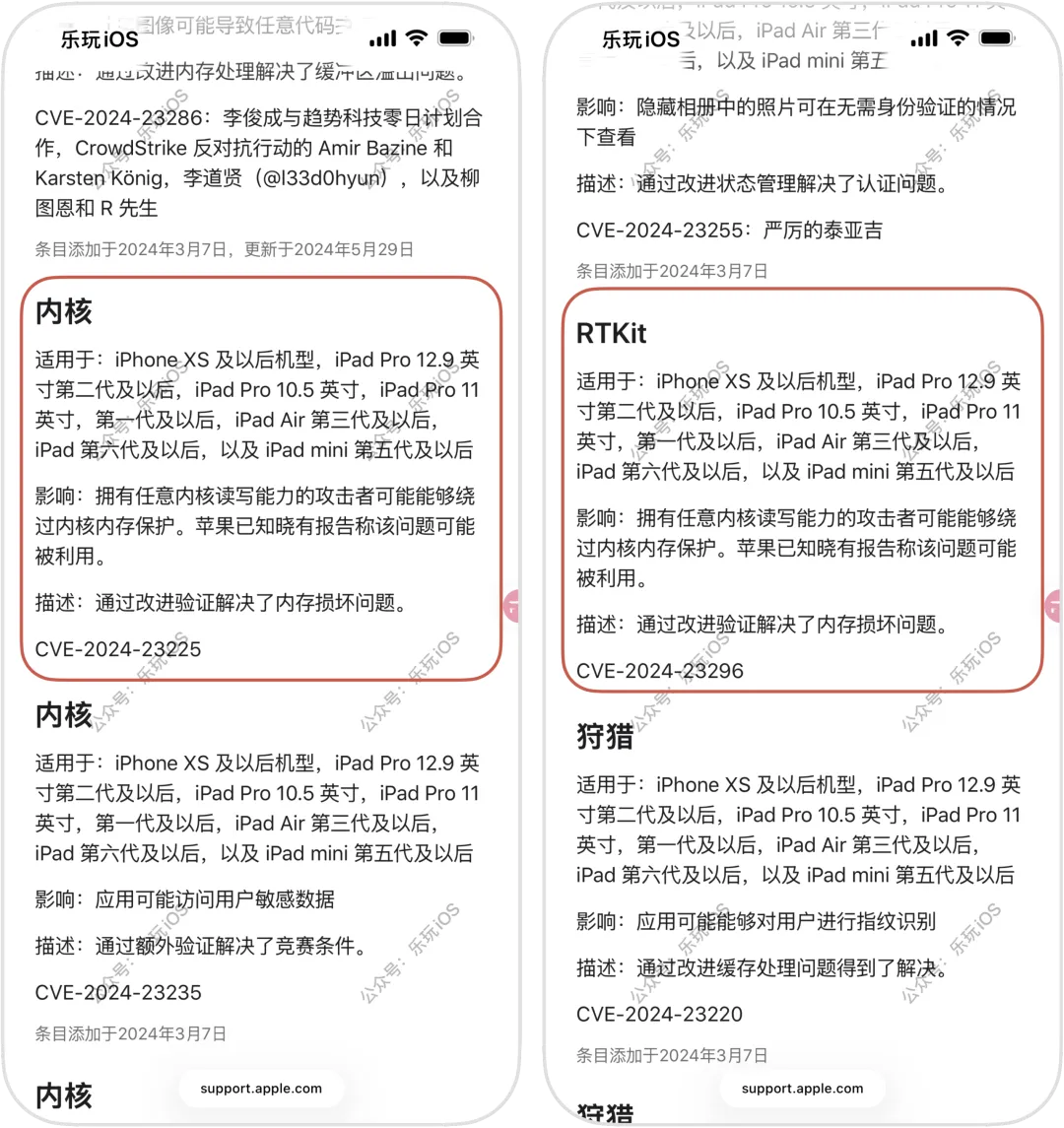
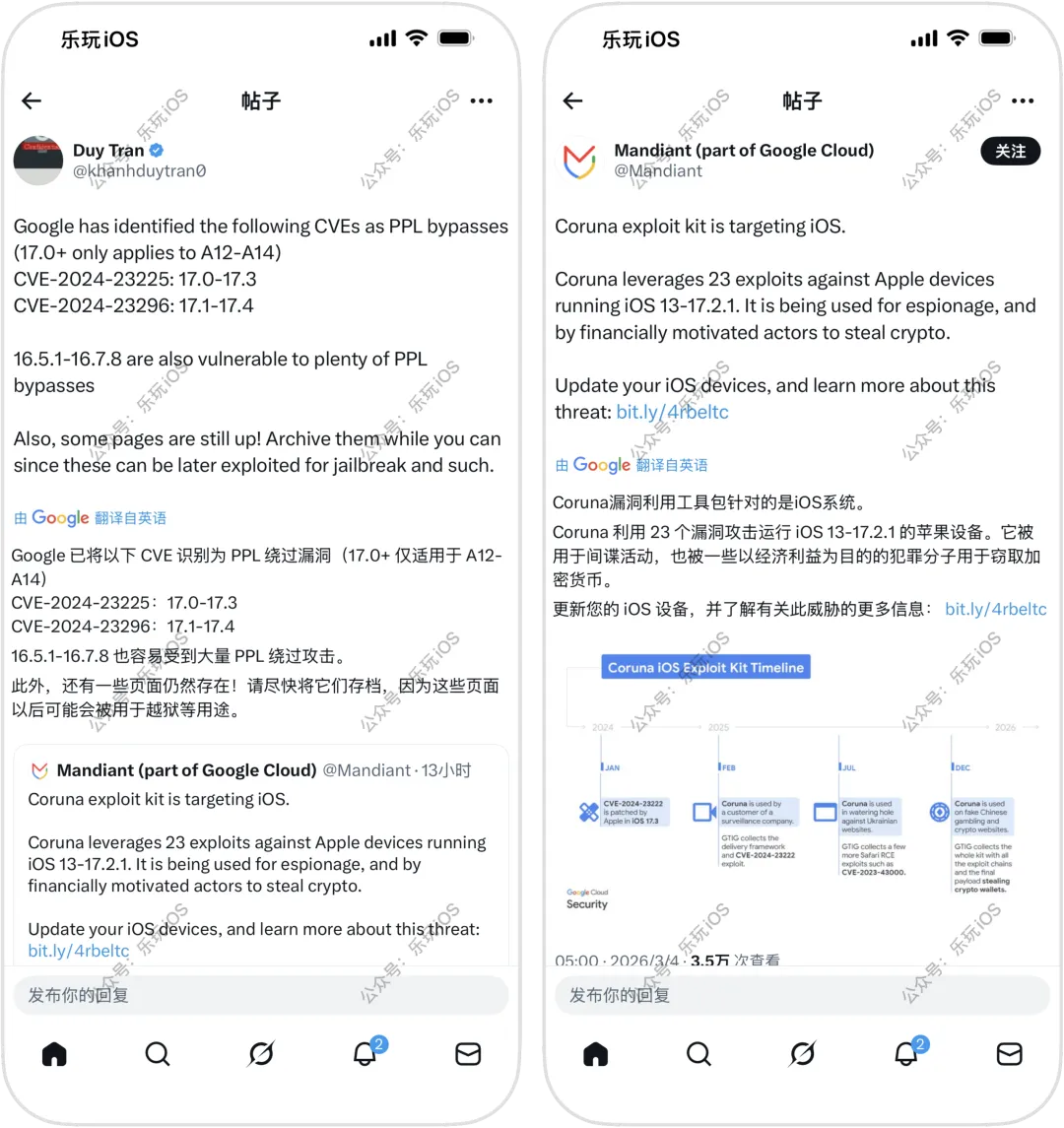
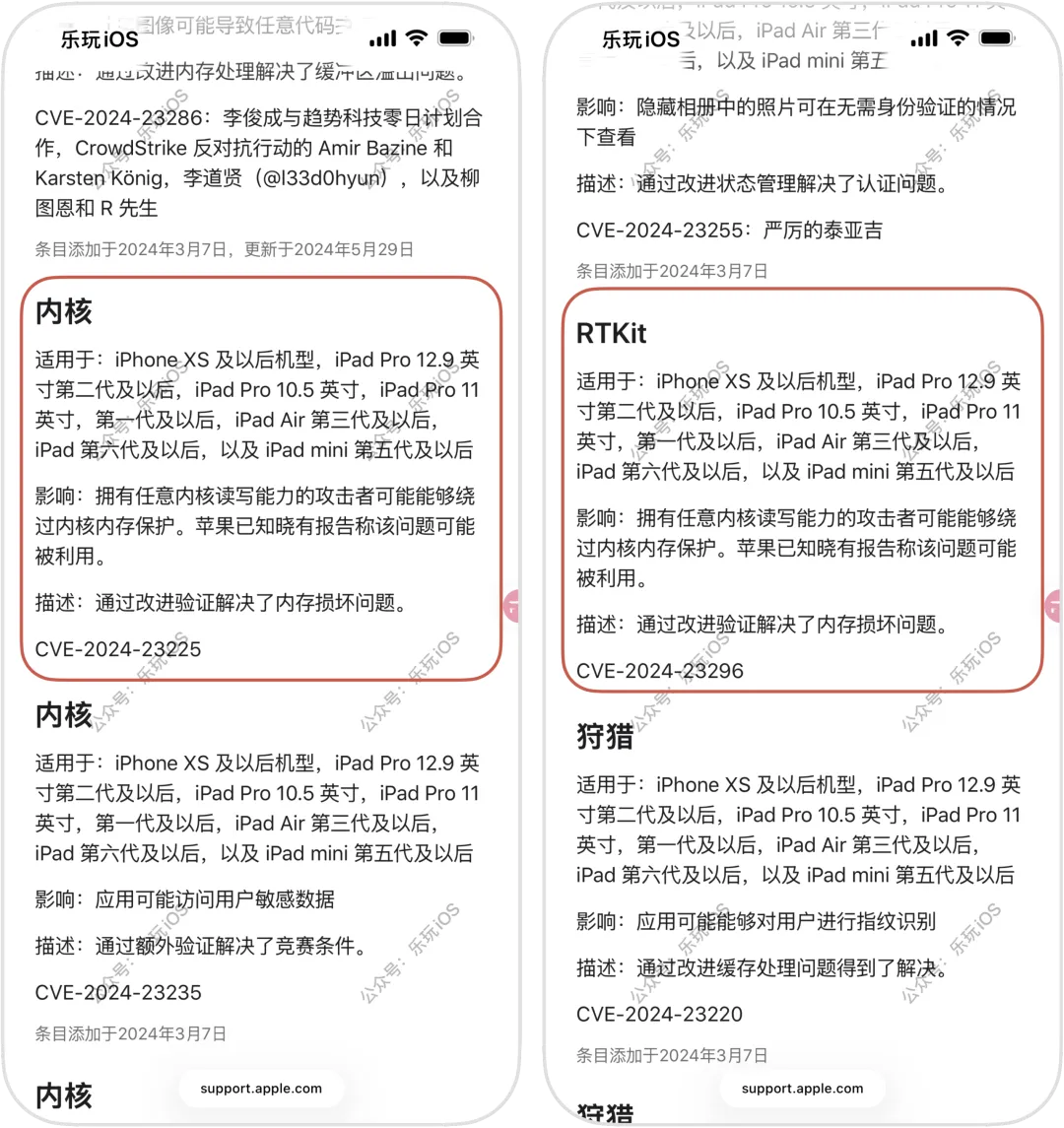
iOS 17 巨魔越狱或有点戏,PPL 漏洞!近日,开发者大佬 Duy Tran 在社媒X上发文称:“Google 已将以下CVE识别为PPL绕过漏洞(17.0+仅适用于A12-A14)16.5.1-16.7.8也容易受到大量PPL绕过攻击。此外,还有一些页面仍然存在!请尽快将它们存档,因为这些页面以后可能会被用于越狱等用途”根据苹果安全文档来看,CVE-2024-23225以及CVE-2024-23296这两个漏洞主要是可以实现绕过内核内存保护结合以上信息,总结下来自大佬Michael 的观点:1、该链式工具包利用的漏洞已在 16.7.6/17.5 版本中全部修复,最后一个内核漏洞也已在 16.7.5/17.2.1 版本中修复2、PPL绕过漏洞适用于A12-A14设备(iPhone XS-iPhone 12)的iOS 17+ 系统3、不过似乎也适用于SPTM设备(A15-A17),可能适用于所有 17.0-17.2.1 版本的设备4、如果存在足够多的漏洞,基于WebKit 越狱实现 TrollStore安装可能可行,即可能实现网页安装巨魔的方法,但仅针对 iOS 17.0 及更低版本,不过能越狱的话,也可能实现安装越狱版巨魔5、当前仅是有了PPL漏洞绕过消息,目前已有研究,但离真正的越狱还远,只能说有了希望▽ 点击下方进入玩机库 ▽

点个赞分享下噢
基本
文件
流程
错误
SQL
调试
- 请求信息 : 2026-03-10 14:22:48 HTTP/1.1 GET : https://www.yeyulingfeng.com/a/461559.html
- 运行时间 : 0.218574s [ 吞吐率:4.58req/s ] 内存消耗:4,723.64kb 文件加载:145
- 缓存信息 : 0 reads,0 writes
- 会话信息 : SESSION_ID=c37aca4647e8d0faed2466103028f3f2
- CONNECT:[ UseTime:0.001020s ] mysql:host=127.0.0.1;port=3306;dbname=wenku;charset=utf8mb4
- SHOW FULL COLUMNS FROM `fenlei` [ RunTime:0.001323s ]
- SELECT * FROM `fenlei` WHERE `fid` = 0 [ RunTime:0.000658s ]
- SELECT * FROM `fenlei` WHERE `fid` = 63 [ RunTime:0.000693s ]
- SHOW FULL COLUMNS FROM `set` [ RunTime:0.001363s ]
- SELECT * FROM `set` [ RunTime:0.000955s ]
- SHOW FULL COLUMNS FROM `article` [ RunTime:0.001633s ]
- SELECT * FROM `article` WHERE `id` = 461559 LIMIT 1 [ RunTime:0.001379s ]
- UPDATE `article` SET `lasttime` = 1773123768 WHERE `id` = 461559 [ RunTime:0.016517s ]
- SELECT * FROM `fenlei` WHERE `id` = 64 LIMIT 1 [ RunTime:0.004650s ]
- SELECT * FROM `article` WHERE `id` < 461559 ORDER BY `id` DESC LIMIT 1 [ RunTime:0.000998s ]
- SELECT * FROM `article` WHERE `id` > 461559 ORDER BY `id` ASC LIMIT 1 [ RunTime:0.001710s ]
- SELECT * FROM `article` WHERE `id` < 461559 ORDER BY `id` DESC LIMIT 10 [ RunTime:0.001630s ]
- SELECT * FROM `article` WHERE `id` < 461559 ORDER BY `id` DESC LIMIT 10,10 [ RunTime:0.001376s ]
- SELECT * FROM `article` WHERE `id` < 461559 ORDER BY `id` DESC LIMIT 20,10 [ RunTime:0.001835s ]

0.224205s