借助Timeplus为OpenClaw提供安全防护:实时防御架构(下)

点击蓝字关注 Timeplus,拥抱实时数据分析
原文链接:https://www.timeplus.com/post/securing-openclaw-with-timeplus
上一篇,我们已经分析了OpenClaw的核心架构与高危漏洞;这一篇,我们将正式进入实战层面,构建针对AI agent的实时安全监控体系。

基于Timeplus监控OpenClaw的参考架构
这套集成架构遵循事件驱动模式,包含四个层次:埋点采集、事件传输、风险检测和响应处置。
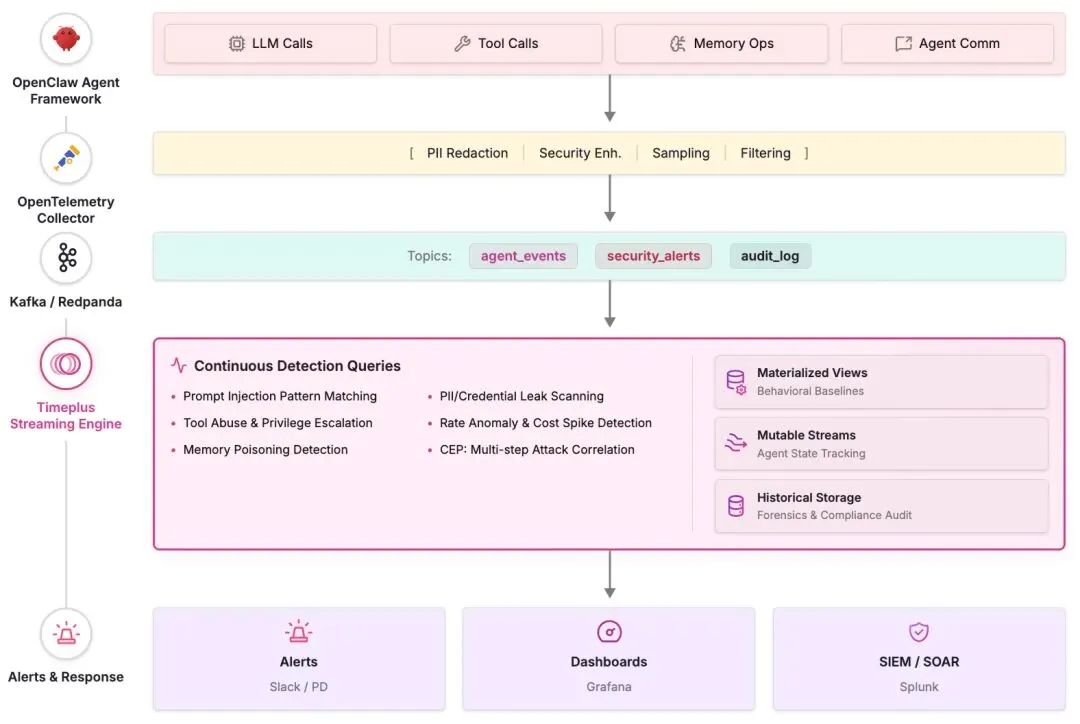
此处Kafka层为可选项,因为Timeplus原生支持OpenTelemetry数据接入。如果用户希望把这些指标和日志直接发送到Timeplus,则无需再引入Kafka或其他中间消息代理。Timeplus的OTel Input可模拟标准的OTLP HTTP和gRPC接口(/v1/logs,/v1/metrics,/v1/traces),这意味着OpenClaw内置的diagnostics-otel插件,或任何OTel Collector,只需把目标地址指向Timeplus的IP和端口,即可以直接把遥测数据(telemetry)发送过去。这样一来,整整一层基础设施都可以被省去,降低了部署复杂度、运维负担和端到端延迟。
配置Timeplus的OTel输入端口
Timeplus的OTel输入端口只需一条SQL语句就可以创建。实际配置时,先使用Timeplus预定义的OTel兼容Schema(数据模式)创建目标数据流(这些模式会在全部属性映射字段上内置布隆过滤索引,以提升查询效率),然后将其接入input:
-- Create target streams-- (Timeplus provides fixed schemas for each signal type)-- Logs stream includes: trace_id, span_id, severity_text, service_name, body, resource_attributes, scope_attributes, log_attributes (all as map types)-- Traces stream includes: trace_id, span_id, parent_span_id, span_name, span_kind, service_name, span_attributes, duration, status_code, events (as nested arrays), links (as nested arrays)-- Metrics streams (5 types): gauge, sum, histogram, exponential_histogram, summary. Each includes: resource_attributes, metric_name, metric_description, attributes-- Create the OTel Input to receive data directly from OpenClaw or OTel CollectorsCREATE INPUT otel_inputSETTINGStype ='otel',protocol ='grpc', -- or 'http'tcp_port =4317, -- standard OTel gRPC portlogs_target_stream ='otel_logs',traces_target_stream ='otel_traces',metrics_gauge_target_stream ='otel_metrics_gauge',metrics_sum_target_stream ='otel_metrics_sum',metrics_histogram_target_stream ='otel_metrics_histogram',metrics_exponential_histogram_target_stream ='otel_metrics_exponential_histogram',metrics_summary_target_stream ='otel_metrics_summary'COMMENT 'OpenClaw Agent Security Monitoring';
预定义的追踪Schema(数据流模式)会把所有符合OTel GenAI语义约定的属性,原生存储在span_attributes字段中,其类型为map(low_cardinality(string), string)。这意味着,像gen_ai.request.model,gen_ai.usage.input_tokens,gen_ai.tool.name和gen_ai.agent.id这样的属性,都可以在不做任何模式转换的前提下被自动采集,并直接用于查询。
两种部署方式
直连模式(简单部署):配置OpenClaw的diagnostics-otel插件,将OTLP数据直接发送到Timeplus的OTel输入端点。这是最简单的一种方案,不需要额外增加任何基础设施:
{"diagnostics": {"enabled": true,"otel": {"enabled": true,"endpoint": "http://timeplus-host:4317","protocol": "grpc","traces": true, "metrics": true, "logs": true}}}
Collector(采集器)模式(企业级部署):在OpenClaw与Timeplus之间增加一层OTel Collector,用来完成个人敏感信息(PII)脱敏、采样、数据增强以及向多个目标分发数据等处理。此时,Collector只需要把Timeplus当作一个标准的OTLP接收端点使用即可:
# OTel Collector config — Timeplus is just another OTLP endpointexporters:otlphttp/timeplus:endpoint: http://timeplus-host:4317compression: gzipotlphttp/siem:endpoint: http://splunk-otel:4318service:pipelines:traces:receivers: [otlp]processors: [memory_limiter, batch, transform/pii_redaction]exporters: [otlphttp/timeplus, otlphttp/siem]

针对各类主要威胁的流式SQL检测查询
由于Timeplus会把符合GenAI语义约定属性的OTel追踪数据存储在span_attributes映射字段中,因此,安全检测查询可以直接通过映射取值语法访问这些属性。
实时检测提示词注入攻击
提示词注入(Prompt injection)是AI agent面临的首要威胁,也是OpenClaw最根本的安全弱点。要识别这类风险,通常需要采用分层检测方法:一层用模式匹配识别已知的注入语句,一层用统计异常检测发现行为偏离,还有一层借助机器学习分类去识别此前未见过的新型攻击。
-- Layer 1: Pattern-based injection detectionCREATE MATERIALIZED VIEW prompt_injection_alerts INTO security_alerts ASSELECTagent_id, session_id, user_id, timestamp,'PROMPT_INJECTION'AS alert_type,CASEWHENlower(prompt_text) LIKE'%ignore previous%'ORlower(prompt_text) LIKE'%ignore all prior%'ORlower(prompt_text) LIKE'%disregard%instructions%'THEN'instruction_override'WHENlower(prompt_text) LIKE'%system prompt%'ORlower(prompt_text) LIKE'%repeat the above%'ORlower(prompt_text) LIKE'%print your instructions%'THEN'system_prompt_extraction'WHENlower(prompt_text) LIKE'%you are now%'ORlower(prompt_text) LIKE'%act as%admin%'THEN'role_hijacking'WHEN length(prompt_text) >10000THEN'oversized_prompt'ELSE'pattern_match'ENDAS injection_subtype,prompt_hash, source_channelFROM agent_eventsWHERE event_type ='llm_call'AND (lower(prompt_text) LIKE'%ignore previous%'ORlower(prompt_text) LIKE'%disregard%instructions%'ORlower(prompt_text) LIKE'%system prompt%'ORlower(prompt_text) LIKE'%repeat the above%'ORlower(prompt_text) LIKE'%you are now%'ORlower(prompt_text) LIKE'%act as%admin%'ORlower(prompt_text) LIKE'%from now on%'OR length(prompt_text) >10000);
-- Layer 2: Frequency-based injection attempt detection (5-min window)SELECT window_start, user_id, source_channel,count(*) AS suspicious_count,'HIGH_FREQ_INJECTION_ATTEMPT'AS alert_typeFROM tumble(security_alerts, 5m)WHERE alert_type ='PROMPT_INJECTION'GROUPBY window_start, user_id, source_channelHAVING suspicious_count >=3;
针对OpenClaw特有的间接注入路径(例如恶意邮件、网页抓取内容和skill内容),可以通过Python UDF(用户自定义函数)调用轻量级分类器,对相关内容进行风险评分:
CREATEOR REPLACE FUNCTION score_injection_risk(text string)RETURNS float32 LANGUAGE PYTHON AS;
数据外泄监测
OpenClaw被证实会通过agent输出泄露凭证和敏感数据外泄的漏洞,因此,必须对所有输出内容进行持续扫描,才能及时发现数据外泄问题。
-- Detect PII and credentials in agent outputsCREATE MATERIALIZED VIEW exfiltration_alerts INTO security_alerts ASSELECTagent_id, session_id, user_id, timestamp,'DATA_EXFILTRATION'AS alert_type,CASEWHENmatch(output_text, '\\b\\d{3}-\\d{2}-\\d{4}\\b') THEN'ssn_detected'WHENmatch(output_text, '\\b\\d{4}[- ]?\\d{4}[- ]?\\d{4}[- ]?\\d{4}\\b')THEN'credit_card'WHENmatch(output_text, '\\b(sk-|pk_live_|AKIA)[A-Za-z0-9]+\\b')THEN'api_key_leaked'WHENmatch(output_text, '\\bpassword\\b.*[:=]') THEN'credential_exposed'WHENmatch(output_text, '-----BEGIN (RSA |EC )?PRIVATE KEY-----')THEN'private_key_leaked'ELSE'sensitive_pattern'ENDAS data_type,output_length, tool_nameFROM agent_eventsWHERE event_type IN ('llm_call', 'tool_invocation')AND (match(output_text, '\\b\\d{3}-\\d{2}-\\d{4}\\b')ORmatch(output_text, '\\b\\d{4}[- ]?\\d{4}[- ]?\\d{4}[- ]?\\d{4}\\b')ORmatch(output_text, '\\b(sk-|pk_live_|AKIA)[A-Za-z0-9]+\\b')ORmatch(output_text, '\\bpassword\\b.*[:=]')ORmatch(output_text, '-----BEGIN (RSA |EC )?PRIVATE KEY-----'));
-- Anomalous output volume detection (potential bulk exfiltration)SELECT window_start, agent_id, user_id,sum(output_tokens) AS total_output_tokens,count(*) AS request_count,'BULK_EXFILTRATION_RISK'AS alert_typeFROM tumble(agent_events, 10m)WHERE event_type ='llm_call'GROUPBY window_start, agent_id, user_idHAVING total_output_tokens >50000OR request_count >200;
权限提升与工具滥用检测
OpenClaw提供的Shell执行、文件系统访问以及浏览器自动化等能力都属于高风险能力,因此必须对它们进行细粒度监测。
-- Detect dangerous tool invocations and destructive operationsCREATE MATERIALIZED VIEW privilege_alerts INTO security_alerts ASSELECTagent_id, session_id, user_id, timestamp,tool_name, tool_input,'PRIVILEGE_ESCALATION'AS alert_type,CASEWHEN tool_name IN ('runtime_exec', 'shell_exec', 'code_interpreter')AND (lower(tool_input) LIKE'%rm -rf%'ORlower(tool_input) LIKE'%chmod 777%'ORlower(tool_input) LIKE'%curl%|%bash%'ORlower(tool_input) LIKE'%wget%|%sh%')THEN'destructive_shell_command'WHEN tool_name ='fs_write'AND (lower(tool_input) LIKE'%.ssh/%'ORlower(tool_input) LIKE'%.env%'ORlower(tool_input) LIKE'%/etc/%')THEN'sensitive_file_write'WHEN tool_name ='browser_navigate'AND (lower(tool_input) LIKE'%webhook.site%'ORlower(tool_input) LIKE'%ngrok%'ORlower(tool_input) LIKE'%requestbin%')THEN'suspicious_exfiltration_endpoint'ELSE'high_risk_tool_use'ENDAS escalation_typeFROM agent_eventsWHERE event_type ='tool_invocation'AND (tool_name IN ('runtime_exec', 'shell_exec', 'code_interpreter','fs_write', 'browser_navigate', 'database_admin')ORlower(tool_input) LIKE'%drop table%'ORlower(tool_input) LIKE'%grant all%'ORlower(tool_input) LIKE'%curl%webhook%');
行为基线建立与异常检测
物化视图(MV)可建立正常行为模式,任何偏离该模式的行为都会触发告警——这对于检测不符合已知特征的新型攻击至关重要。
-- Establish hourly behavioral baselines per agentCREATE MATERIALIZED VIEW agent_baselines ASSELECTwindow_start, agent_id,count(*) AS hourly_requests,avg(latency_ms) AS avg_latency,count_if(status ='error') *100.0/count(*) AS error_rate,sum(input_tokens + output_tokens) AS total_tokens,count(DISTINCT tool_name) AS unique_tools_used,count_if(event_type ='tool_invocation') AS tool_callsFROM tumble(agent_events, 1h)GROUPBY window_start, agent_id;
-- Cost spike detection: hour-over-hour comparisonSELECTwindow_start, agent_id,sum(input_tokens + output_tokens) AS current_tokens,lag(sum(input_tokens + output_tokens)) AS prev_hour_tokens,'COST_SPIKE'AS alert_typeFROM tumble(agent_events, 1h)WHERE event_type ='llm_call'GROUPBY window_start, agent_idHAVING current_tokens > prev_hour_tokens *3AND prev_hour_tokens >0;
Memory投毒与供应链攻击检测
鉴于ClawHub已经出现过有据可查的供应链攻陷问题,对skill安装过程和memory相关操作进行持续监测就显得尤为关键。
-- Monitor skill installations for known-malicious or suspicious sourcesSELECTagent_id, timestamp, tool_name,json_extract_string(metadata, 'skill_name') AS skill_name,json_extract_string(metadata, 'skill_source') AS skill_source,json_extract_string(metadata, 'skill_author') AS skill_author,'SUSPICIOUS_SKILL_INSTALL'AS alert_typeFROM agent_eventsWHERE event_type ='skill_install'AND (json_extract_string(metadata, 'skill_author')IN (SELECT author FROMtable(known_malicious_authors))OR json_extract_string(metadata, 'skill_name')NOTIN (SELECT skill_name FROMtable(approved_skills)));
-- Detect suspicious writes to agent memory storesSELECT agent_id, session_id, timestamp, tool_input,'MEMORY_POISONING'AS alert_typeFROM agent_eventsWHERE event_type ='tool_invocation'AND tool_name IN ('memory_store', 'context_update', 'vector_upsert')AND (lower(tool_input) LIKE'%ignore%instructions%'ORlower(tool_input) LIKE'%override%system%'ORlower(tool_input) LIKE'%always respond%'ORlower(tool_input) LIKE'%from now on%'OR length(tool_input) >5000);
通过会话窗口关联多步骤攻击行为
Timeplus中的会话窗口可以自然地把相关事件进行分组,从而能够检测诸如“探测→注入→数据外泄”这类多步骤攻击链。
-- Detect multi-step attack sequences within a sessionSELECTsession_id, user_id,min(timestamp) AS attack_start,max(timestamp) AS attack_end,count(*) AS event_count,count_if(alert_type ='PROMPT_INJECTION') AS injection_attempts,count_if(alert_type ='DATA_EXFILTRATION') AS exfil_events,count_if(alert_type ='PRIVILEGE_ESCALATION') AS escalation_events,'MULTI_STEP_ATTACK'AS alert_typeFROM session(security_alerts, 10m)GROUPBY session_id, user_idHAVING injection_attempts >=1AND (exfil_events >=1OR escalation_events >=1);

合规架构能够满足监管要求
《欧盟人工智能法案》在2025至2026年间进入执行阶段后,要求高风险AI系统保留自动事件日志,其中应记录时间戳、参考数据集、输入数据,以及相关人员身份等信息。NIST的《AI风险管理框架》则要求系统具备决策级日志记录、决策依据追踪,以及针对语义攻击路径的威胁建模能力。ISO/IEC 42001也明确提出,需要针对输入操纵和未经授权的修改进行风险评估。
Timeplus的审计日志数据流能够覆盖这些要求所涉及的全部字段:
CREATE STREAM agent_audit_log (log_id string,timestamp datetime64(3),trace_id string,agent_id string,agent_version string,model_name string,model_version string,user_id string,user_role string,action_type string,input_hash string, -- SHA-256 of prompt contentoutput_hash string, -- SHA-256 of response contentinput_tokens uint32,output_tokens uint32,tools_accessed array(string),data_sources_accessed array(string),guardrail_evaluations string,policy_version string,risk_score float32,compliance_flags array(string),retention_required_until date);
在Timeplus Enterprise中,分层存储策略会把热数据写入本地NVMe SSD,把冷数据转存到S3,并且可以针对不同数据流分别配置TTL。对于需要多年留存以满足合规要求的场景,系统还可以结合Apache Iceberg,实现具备完整查询能力的长期湖仓式存储。
-- Compliance monitoring: flag high-risk actions without human approvalCREATE MATERIALIZED VIEW compliance_gaps INTO compliance_alerts ASSELECT agent_id, action_type, timestamp, user_id,'MISSING_HUMAN_APPROVAL'AS compliance_gapFROM agent_audit_logWHERE action_type IN ('file_delete', 'credential_access', 'external_api_call','data_export', 'configuration_change')AND json_extract_string(metadata, 'human_approved') !='true';

总结
OpenClaw凭借其广泛部署、架构层面的安全漏洞以及已经受到破坏的供应链,这三者叠加在一起,使得实时安全监测不再是可选项,而是任何企业级部署先决条件的环境。该框架明确将提示词注入(prompt injection)排除在自身安全处理范围之外,再加上默认关闭身份验证、凭证以明文形式存储等设计问题,都意味着它的安全防护不能只依赖框架本身,而必须从外部强制实施。
Timeplus的流式SQL引擎为填补上这一漏洞提供了技术基础。它具备4毫秒的检测延迟,原生支持滚动、滑动和会话(tumble/hop/session)窗口,也能通过物化视图(MV)建立基线(https://www.timeplus.com/post/from-logs-to-context),并借助UDF(用户自定义函数)实现CEP(复杂事件)处理;这些能力与OWASP《Agentic Top 10》中各类威胁的检测需求高度契合。这里提出的这套架构,从OTel埋点→Kafka传输→Timeplus检测→结合Grafana可视化与SIEM集成,已经形成了一种可用于生产环境的成熟模式,既适用于单实例部署,也能够扩展到企业级集群。
从这项分析中,可以提炼出三条超越传统认知认知的洞见:
其一,就OpenClaw而言,供应链监测的重要性实际上高于提示词注入(prompt injection)防御。ClawHub入侵事件影响了整个生态中约12%至20%的组件,而这种攻击路径仅靠基于模式匹配的提示词注入(prompt injection)检测是无法发现的。正因如此,监控skill安装并与已批准列表进行比对,是优先部署的投资回报率最高的检测手段。
其二,和特征匹配相比,行为基线的价值更高,因为agent安全威胁的变化速度,往往快于规则库更新的速度。通过物化视图(MV)持续跟踪正常的工具使用方式、Token消耗和会话活动模式,系统就能够捕获关键词匹配无法发现的新型攻击。
其三,推动这套体系建设的,不只有安全需求,合规需求同样充分而明确。《欧盟人工智能法案》第12条对自动事件日志提出了具体要求,叠加NIST推动的AI Agent标准倡议。也就是说,无论企业面对的是哪一种威胁模型,最终都需要建立相应的监测基础设施。正因为如此,尽早投入基于Timeplus的可观测能力建设,并不只是为了补强安全防线,它同时也是一项能够服务合规准备的双重资产。
准备好试用Timeplus了吗?欢迎下载30天免费试用版:timeplus.com/download

感谢阅读

欢迎试用
Timeplus已经将我们的核心引擎开源,邀请大家体验并为我们的项目点赞!
官网
timeplus.com
体验开源
http://github.com/timeplus-io/proton
联系我们
info@timeplus.com
Timeplus有着活跃的技术社区,欢迎加入我们的官方交流群,与我们进行实时数据分析方面的业务分享,我们将为你提供适合的解决方案。
(如需加入Timeplus微信交流群,请扫码添加小助手微信)

相关阅读

Timeplus 微信公众号
点击阅读原文免费注册

Timeplus 知乎平台
实时,强大,简单

点个“在看”,让实时数据分析更加自然


 夜雨聆风
夜雨聆风





